.NET Training Classes in Dover, Delaware
Learn .NET in Dover, Delaware and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current .NET related training offerings in Dover, Delaware: .NET Training
.NET Training Catalog
subcategories
C# Programming Classes
Design Patterns Classes
F# Programming Classes
JUnit, TDD, CPTC, Web Penetration Classes
Microsoft Development Classes
Microsoft Windows Server Classes
SharePoint Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Linux Fundaments GL120
15 July, 2024 - 19 July, 2024 - VMware vSphere 8.0 Boot Camp
10 June, 2024 - 14 June, 2024 - RED HAT ENTERPRISE LINUX AUTOMATION WITH ANSIBLE
3 June, 2024 - 6 June, 2024 - VMware vSphere 8.0 with ESXi and vCenter
10 June, 2024 - 14 June, 2024 - Docker
29 April, 2024 - 1 May, 2024 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
 One of the biggest challenges faced by senior IT professionals in organizations is the choice of the right software vendor. In the highly competitive enterprise software industry, there are lot of vendors who claim to offer the best software for the problem and it can be really daunting to narrow down the best choice. Additionally, enterprise software costs can often run into millions of dollars thereby leaving very little margin of error. The real cost of choosing a wrong software can often result into losses much more than the cost of the software itself as highlighted by software disasters experienced by leading companies like HP, Nike etc. In such a scenario, senior IT professionals despite years of expertise can find it very difficult to choose the right business software vendor for their organization.
One of the biggest challenges faced by senior IT professionals in organizations is the choice of the right software vendor. In the highly competitive enterprise software industry, there are lot of vendors who claim to offer the best software for the problem and it can be really daunting to narrow down the best choice. Additionally, enterprise software costs can often run into millions of dollars thereby leaving very little margin of error. The real cost of choosing a wrong software can often result into losses much more than the cost of the software itself as highlighted by software disasters experienced by leading companies like HP, Nike etc. In such a scenario, senior IT professionals despite years of expertise can find it very difficult to choose the right business software vendor for their organization.
Here are some of the proven ways of short-listing and selecting the right business software vendor for your organization,
· Understand and Define The Exact Need First: Before embarking on a journey to select the software vendor, it is critical to understand and define the exact problem you want the software to solve. The paramount question to be asked is what business objective does the software need to solve. Is the software required to “reduce costs” or is it to “improve productivity”? Extracting and defining this fundamental question is the bare minimum but necessary step to go searching for the right vendor. It will then form the basis of comparing multiple vendors on this very need that your organization has and will help drive the selection process going forward. The detailed approach involves creating a set of parameters that the software needs to meet in order to be considered. In fact, consider categorizing these parameters further in “must-haves”, “good to have” etc. which will help you assign relevant weights to these parameter and how the software’s fare on each of these parameters
· Building The List of Vendors Who Meet The Need: Once you have defined your need and distilled that need into various parameters, it’s time to built the list of vendors who you think will meet the need. This is akin to a lead generation model wherein you want to identify a large enough pool and then filters your list down to the best ones. There are multiple ways of building a list of vendors and more often than not, you must use a combination of these methods to build a good enough list.
o Use Industry Reports: We discussed the IT intelligence offered by leading industry firms Gartner and Forrester in How To Keep On Top Of Latest Trends In Information Technology. These firms based on their access to leading software vendors and CIO network publish vendor comparison research reports across specific verticals as well as specific technologies. Gartner’s Magic Quadrant and Forrester’s Wave are a very good starting point to get an insight into the best software vendors. For example, if you were looking for a CRM solution, you could look for Gartner’s Magic Quadrant for CRM and look at the vendors that make the list. These reports can be pricey but well worth the money if you are going to invest hundreds of thousands in the software. Having said that, you don’t have to trust these report blindly because how these firms define the best software may not match how you define the best software for your organization
o Competitive Intelligence: If you are a smart professional, you are already keeping tabs of your competition. Chances are that if you are a big organization, you might see a Press Release either from your competitor or their vendor announcing the implementation of new software. Extrapolate that across 5-10 key competitors of yours and you might discover the vendors that your competitors are choosing. This gives you a good indicator that the vendors used by your competitors must be offering something right.
 In programming, memory leaks are a common issue, and it occurs when a computer uses memory but does not give it back to the operating system. Experienced programmers have the ability to diagnose a leak based on the symptoms. Some believe every undesired increase in memory usage is a memory leak, but this is not an accurate representation of a leak. Certain leaks only run for a short time and are virtually undetectable.
In programming, memory leaks are a common issue, and it occurs when a computer uses memory but does not give it back to the operating system. Experienced programmers have the ability to diagnose a leak based on the symptoms. Some believe every undesired increase in memory usage is a memory leak, but this is not an accurate representation of a leak. Certain leaks only run for a short time and are virtually undetectable.
Memory Leak Consequences
Applications that suffer severe memory leaks will eventually exceed the memory resulting in a severe slowdown or a termination of the application.
How to Protect Code from Memory Leaks?
Preventing memory leaks in the first place is more convenient than trying to locate the leak later. To do this, you can use defensive programming techniques such as smart pointers for C++. A smart pointer is safer than a raw pointer because it provides augmented behavior that raw pointers do not have. This includes garbage collection and checking for nulls.
If you are going to use a raw pointer, avoid operations that are dangerous for specific contexts. This means pointer arithmetic and pointer copying. Smart pointers use a reference count for the object being referred to. Once the reference count reaches zero, the excess goes into garbage collection. The most commonly used smart pointer is shared_ptr from the TR1 extensions of the C++ standard library.
Static Analysis
The second approach to memory leaks is referred to as static analysis and attempts to detect errors in your source-code. CodeSonar is one of the effective tools for detection. It provides checkers for the Power of Ten coding rules, and it is especially competent at procedural analysis. However, some might find it lagging for bigger code bases.
How to Handle a Memory Leak
For some memory leaks, the only solution is to read through the code to find and correct the error. Another one of the common approaches to C++ is to use RAII, which an acronym for Resource Acquisition Is Initialization. This approach means associating scoped objects using the acquired resources, which automatically releases the resources when the objects are no longer within scope. RAII has the advantage of knowing when objects exist and when they do not. This gives it a distinct advantage over garbage collection. Regardless, RAII is not always recommended because some situations require ordinary pointers to manage raw memory and increase performance. Use it with caution.
The Most Serious Leaks
Urgency of a leak depends on the situation, and where the leak has occurred in the operating system. Additionally, it becomes more urgent if the leak occurs where the memory is limited such as in embedded systems and portable devices.
To protect code from memory leaks, people have to stay vigilant and avoid codes that could result in a leak. Memory leaks continue until someone turns the system off, which makes the memory available again, but the slow process of a leak can eventually prejudice a machine that normally runs correctly.
Related:
It is hard not to wonder how current technology would have altered the events surrounding the tragic death of John F. Kennedy. On the afternoon of November 22, 1963, shots rang out in Dallas, TX, taking the life of JFK, one of the most beloved Americans. Given the same circumstances today, surely the advances in IT alone, would have drastically changed the outcome of that horrible day. Would the government have recognized that there was a viable threat looming over JFK? Would local and government agencies have been more prepared for a possible assassination attempt? Would the assortment of everyday communication devices assisted in the prevention of the assassination, not to mention, provided greater resources into the investigation? With all that the IT world has to offer today, how would it have altered the JFK tragedy?
As many conspiracy theories have rocked the foundation of the official story presented by government agencies, realization of the expansive nature of technology provides equal consideration as to how the event would have been changed had this technology been available during the time of the shooting. There were T.V. cameras, home 8mm recorders, even single shot-hand held cameras snapping away as the car caravan approached. Yet, there remains little documentation of the shooting and even less information pertaining to the precautions taken by officials prior to JFK's arrival. Theorists consider these possibilities along with how the world would have turned out had the great John F. Kennedynever been assassinated on that day.
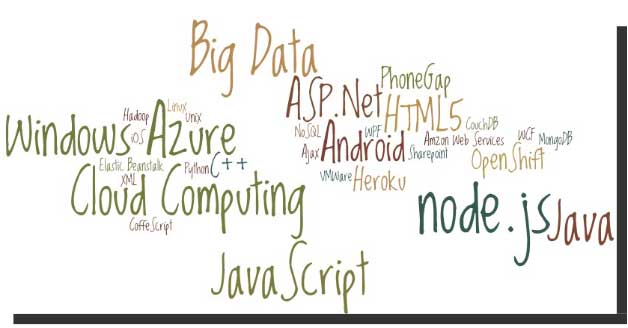
Before we go to the list do you know what makes software skills most sought-after and hence more valuable than most of the other job skills? It is simply because unlike any other skill, software skills are global and are not at all location specific! With the evolution and penetration of internet technologies, the physical distance between the client and service provider hardly matters. So, with more advancement in technology, it is indeed going to rain opportunities on the right skilled developer. I’ll take the liberty to reproduce the following quotes here to prove my claims statistically:
Demand for “cloud-ready” IT workers will grow by 26 percent annually through 2015, with as many as 7 million cloud-related jobs available worldwide.
---IDC White Paper (November 2012).
In the United States, the IT sector is experiencing modest growth of IT jobs in general, with the average growth in IT employment between 1.1 and 2.7 percent per year through 2020.
---U.S. Bureau of Labor Statistics.
Tech Life in Delaware
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Delphi Financial Group, Inc. | Wilmington | Financial Services | Insurance and Risk Management |
| DuPont | Wilmington | Manufacturing | Manufacturing Other |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Delaware since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about .NET programming
- Get your questions answered by easy to follow, organized .NET experts
- Get up to speed with vital .NET programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…










![Cea-Comptia Dhti+ Digital Home Technology Integrator All-In-One Exam Guide, Second Edition [With CDROM]](/bookim/9780071546652.jpg)