IBM Training Classes in Bielefeld, Germany
Learn IBM in Bielefeld, Germany and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current IBM related training offerings in Bielefeld, Germany: IBM Training
IBM Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC (VS2022)
6 October, 2025 - 7 October, 2025 - Introduction to Spring 6, Spring Boot 3, and Spring REST
15 December, 2025 - 19 December, 2025 - RHCSA EXAM PREP
17 November, 2025 - 21 November, 2025 - Object Oriented Analysis and Design Using UML
20 October, 2025 - 24 October, 2025 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
8 December, 2025 - 11 December, 2025 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
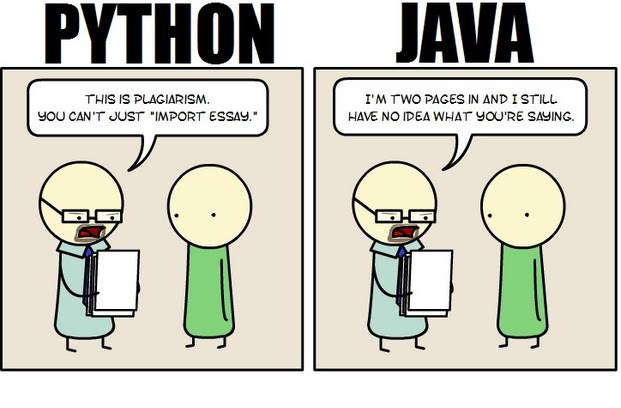 Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
First, Java is a static typed language while Python is dynamically typed. Static typed languages require that each variable name must be tied to both a type and an object. Dynamically typed languages only require that a variable name only gets bound to an object. Immediately, this puts Python ahead of the game in terms of productivity since a static typed language requires several elements and can make errors in coding more likely.
Python uses a concise language while Java uses verbose language. Concise language, as the name suggests, gets straight to the point without extra words. Removing additional syntax can greatly reduce the amount of time required to program. A simple call in Java, such as the ever notorious "Hello, World" requires three several lines of coding while Python requires a single sentence. Java requires the use of checked exceptions. If the exceptions are not caught or thrown out then the code fails to compile. In terms of language, Python certainly has surpassed Java in terms of brevity.
Additionally, while Java's string handling capabilities have improved they haven't yet matched the sophistication of Python's. Web applications rely upon fast load times and extraneous code can increase user wait time. Python optimizes code in ways that Java doesn't, and this can make Python a more efficient language. However, Java does run faster than Python and this can be a significant advantage for programmers using Java. When you factor in the need for a compiler for Java applications the speed factor cancels itself out leaving Python and Java at an impasse.
While a programmer will continue to argue for the language that makes it easiest based on the programmer's current level of knowledge, new software compiled with Python takes less time and provides a simplified coding language that reduces the chance for errors. When things go right, Java works well and there are no problems. However, when errors get introduced into the code, it can become extremely time consuming to locate and correct those errors. Python generally uses less code to begin with and makes it easier and more efficient to work with.
Ultimately, both languages have their own strengths and weaknesses. For creating simple applications, Python provides a simpler and more effective application. Larger applications can benefit from Java and the verbosity of the code actually makes it more compatible with future versions. Python code has been known to break with new releases. Ultimately, Python works best as a type of connecting language to conduct quick and dirty work that would be too intensive when using Java alone. In this sense, Java is a low-level implementation language. While both languages are continuing to develop, it's unlikely that one language will surpass the other for all programming needs in the near future.
 IT jobs are without a doubt some of the highest paying jobs with information architects, data-security analysts and UX designers taking home $100,000 or more a year. But then again, these are high demand; high expertise jobs so don’t jump with joy as yet. But like every job and IT industry to be specific, not everyone commands such higher salaries. There are a large number of IT professionals who at some point of their career feel that their salaries have hit a standstill. Even if you are an IT professional and a great one at that, your technical expertise alone may not help you exceed the IT earning barrier. To continuously exceed your salaries, you need to work hard and smart. Here is how you can exceed the earning barrier in IT.
IT jobs are without a doubt some of the highest paying jobs with information architects, data-security analysts and UX designers taking home $100,000 or more a year. But then again, these are high demand; high expertise jobs so don’t jump with joy as yet. But like every job and IT industry to be specific, not everyone commands such higher salaries. There are a large number of IT professionals who at some point of their career feel that their salaries have hit a standstill. Even if you are an IT professional and a great one at that, your technical expertise alone may not help you exceed the IT earning barrier. To continuously exceed your salaries, you need to work hard and smart. Here is how you can exceed the earning barrier in IT.
· Gain Business Knowledge and Move Up The Management Ladder: IT departments for the most part are considered a part of “back office” operations. What this means is that despite being a core part of the business, IT professionals do not often get enough say in revenue generating components of the business and as a result seldom have a chance to take up senior management roles. So if you do not want to stay content with a project manager or senior project management salary, invest time and money in gaining business knowledge. It could be through a formal business degree, online training courses or just by keeping your eyes and ears open while in the organization. Having the technical experience with business knowledge will instantly make you stand apart and open the doors for you to draw senior management salaries. For example, a survey conducted highlighted that CIOs were the biggest salary winners which clearly demonstrates the value of technical and business knowledge
· Gain expertise on the “Hot” Technologies and Keep Learning: Say you are an expert in Java and draw a respectable salary in the industry. However, someone with less years of experience than you joins the organization and draws a higher salary than you! Why you ask. It could very well be because he/she is an expert in say big data technology such as Hadoop. Information Technology is one of the most dynamic industries with new technologies and languages coming up every now and then. When a new technology comes to the foray and gains traction, there is an instant demand-supply gap created which means that those with the specific skill sets are in a position to demand high salaries. If you have to break the IT earning barrier, always be ready to reinvent yourself by learning new technologies and this way you will be well positioned to jump on the high paying opportunities in the IT industry
· Work On Your Own Side Projects: This one might seem controversial but let me clarify that I do not mean doing freelance work because even though your organization may never find out, it is ethically in breach of contract with your contract. If you have been lucky enough to be trained in some web based technologies such as Java, .NET or even HTML etc. spare sometime after office to build your own side projects. They could be very small projects tackling some problem that only you might have but there are multiple benefits of developing side projects. Worst case scenario, you will improve your technical skills. On the up side, you might end up creating your own business. A lot of technology start-ups were actually side projects the founders tinkered on with while they were employed full-time. You may not always succeed but there is no downside to the same
If you’re interested in building modern websites or applications which use ASP, XML, or mobile technology, you’ve heard of Visual Studio .NET. It is one of the more popular suites of development tools available to aspiring programmers, as it consolidates several different tools and languages into the same development environment, which helps in turn to integrate this code across development languages. Here are three important benefits to using the visual studio suite:
· Use of Visual J# - This development tool is specifically oriented towards people who already are familiar with basic Java syntax, and is designed for use by those people to build apps or services which will then run on the Microsoft .NET Framework. This is useful because it fully supports Microsoft Extensions, among other reasons. Visual J# was developed completely independently by Microsoft.
· Utility for Smart Devices – Another huge benefit of using visual studio .NET is the ability to immediately integrate your programming efforts with deployment across a variety of smart devices. PDAs, smartphones, Pocket PCs, and any device which has a limited amount of resources all require a compact framework for the programming of applications it is designed to run.
· XML Web Usage and Support – Because XML services aren’t married to any particular technology or programming language, they can be accessed by any system, and this broad-based utility has made the services increasingly popular. Visual Studio .NET takes advantage of this by fully integrating with XML services, including the ability to create and edit them from scratch.
Many of us who have iPhones download every interesting app we find on the App Store, especially when they’re free. They can range from a simple payment method app, to a game, to a measurement tool. But, as you may have noticed, our phones become cluttered with tons of pages that we have to swipe through to get to an app that we need on demand. However, with an update by Apple that came out not so long ago, you are able to group your applications into categories that are easily accessible, for all of you organization lovers.
To achieve this grouping method, take a hold of one of the applications you want to categorize. Take a game for example. What you want to do is press your finger on that particular application, and hold it there until all of the applications on the screen begin to jiggle. This is where the magic happens. Drag it over to another game application you want to have in the same category, and release. Your applications should now be held in a little container on your screen. However, a step ago, if you did not have another game application on the same screen, and since you can’t swipe, try putting the held game application on any application you choose, and simply remove that extra application from the list, after moving over another gaming application from a different page.
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Germany since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about IBM programming
- Get your questions answered by easy to follow, organized IBM experts
- Get up to speed with vital IBM programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…