IBM Training Classes in Casper, Wyoming
Learn IBM in Casper, Wyoming and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current IBM related training offerings in Casper, Wyoming: IBM Training
IBM Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - Linux Troubleshooting
1 June, 2026 - 5 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
What is computer crime? Computer crime, often called “cyber crime” is any type of illegal activity that takes place on a computer with a network. Oftentimes, when you think of computer crime, you might picture a home user downloading a virus that wipes out his hard drive or spyware that hijacks her system for the purposes of spying.
Computer crimes can also affect businesses too and they do, sometimes with devastating results. For example, in 2012, the IRS paid a whopping 5.2 billion dollars in tax refunds to identity thieves!
Protect your business and improve your bottom line by staying one step ahead of the cybercriminals.
5 Common Computer Crimes
Let’s face it, fad or not, companies are starting to ask themselves how they could possibly use machine learning and AI technologies in their organization. Many are being lured by the promise of profits by discovering winning patterns with algorithms that will enable solid predictions… The reality is that most technology and business professionals do not have sufficient understanding of how machine learning works and where it can be applied. For a lot of firms, the focus still tends to be on small-scale changes instead of focusing on what really matters…tackling their approach to machine learning.
In the recent Wall Street Journal article, Machine Learning at Scale Remains Elusive for Many Firms, Steven Norton captures interesting comments from the industry’s data science experts. In the article, he quotes panelists from the MIT Digital Economy Conference in NYC, on businesses current practices with AI and machine learning. All agree on the fact that, for all the talk of Machine Learning and AI’s potential in the enterprise, many firms aren’t yet equipped to take advantage of it fully.
Panelist, Michael Chui, partner at McKinsey Global Institute states that “If a company just mechanically says OK, I’ll automate this little activity here and this little activity there, rather than re-thinking the entire process and how it can be enabled by technology, they usually get very little value out of it. “Few companies have deployed these technologies in a core business process or at scale.”
Panelist, Hilary Mason, general manager at Cloudera Inc., had this to say, “With very few exceptions, every company we work with wants to start with a cost-savings application of automation.” “Most organizations are not set up to do this well.”
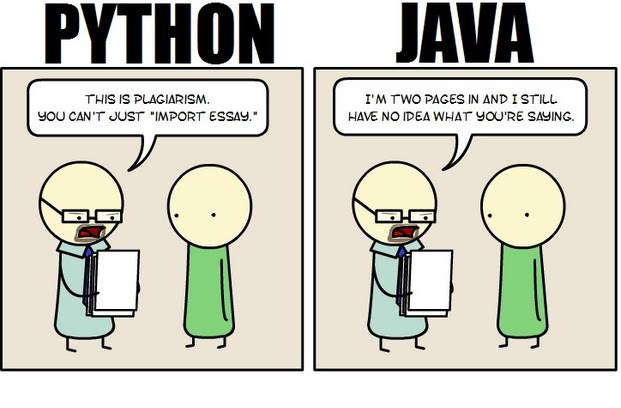 Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
First, Java is a static typed language while Python is dynamically typed. Static typed languages require that each variable name must be tied to both a type and an object. Dynamically typed languages only require that a variable name only gets bound to an object. Immediately, this puts Python ahead of the game in terms of productivity since a static typed language requires several elements and can make errors in coding more likely.
Python uses a concise language while Java uses verbose language. Concise language, as the name suggests, gets straight to the point without extra words. Removing additional syntax can greatly reduce the amount of time required to program. A simple call in Java, such as the ever notorious "Hello, World" requires three several lines of coding while Python requires a single sentence. Java requires the use of checked exceptions. If the exceptions are not caught or thrown out then the code fails to compile. In terms of language, Python certainly has surpassed Java in terms of brevity.
Additionally, while Java's string handling capabilities have improved they haven't yet matched the sophistication of Python's. Web applications rely upon fast load times and extraneous code can increase user wait time. Python optimizes code in ways that Java doesn't, and this can make Python a more efficient language. However, Java does run faster than Python and this can be a significant advantage for programmers using Java. When you factor in the need for a compiler for Java applications the speed factor cancels itself out leaving Python and Java at an impasse.
While a programmer will continue to argue for the language that makes it easiest based on the programmer's current level of knowledge, new software compiled with Python takes less time and provides a simplified coding language that reduces the chance for errors. When things go right, Java works well and there are no problems. However, when errors get introduced into the code, it can become extremely time consuming to locate and correct those errors. Python generally uses less code to begin with and makes it easier and more efficient to work with.
Ultimately, both languages have their own strengths and weaknesses. For creating simple applications, Python provides a simpler and more effective application. Larger applications can benefit from Java and the verbosity of the code actually makes it more compatible with future versions. Python code has been known to break with new releases. Ultimately, Python works best as a type of connecting language to conduct quick and dirty work that would be too intensive when using Java alone. In this sense, Java is a low-level implementation language. While both languages are continuing to develop, it's unlikely that one language will surpass the other for all programming needs in the near future.
Over time, companies are migrating from COBOL to the latest standard of C# solutions due to reasons such as cumbersome deployment processes, scarcity of trained developers, platform dependencies, increasing maintenance fees. Whether a company wants to migrate to reporting applications, operational infrastructure, or management support systems, shifting from COBOL to C# solutions can be time-consuming and highly risky, expensive, and complicated. However, the following four techniques can help companies reduce the complexity and risk around their modernization efforts.
All COBOL to C# Solutions are Equal
It can be daunting for a company to sift through a set of sophisticated services and tools on the market to boost their modernization efforts. Manual modernization solutions often turn into an endless nightmare while the automated ones are saturated with solutions that generate codes that are impossible to maintain and extend once the migration is over. However, your IT department can still work with tools and services and create code that is easier to manage if it wants to capitalize on technologies such as DevOps.
Narrow the Focus
Most legacy systems are incompatible with newer systems. For years now, companies have passed legacy systems to one another without considering functional relationships and proper documentation features. However, a detailed analysis of databases and legacy systems can be useful in decision-making and risk mitigation in any modernization effort. It is fairly common for companies to uncover a lot of unused and dead code when they analyze their legacy inventory carefully. Those discoveries, however can help reduce the cost involved in project implementation and the scope of COBOL to C# modernization. Research has revealed that legacy inventory analysis can result in a 40% reduction of modernization risk. Besides making the modernization effort less complex, trimming unused and dead codes and cost reduction, companies can gain a lot more from analyzing these systems.
Understand Thyself
For most companies, the legacy system entails an entanglement of intertwined code developed by former employees who long ago left the organization. The developers could apply any standards and left behind little documentation, and this made it extremely risky for a company to migrate from a COBOL to C# solution. In 2013, CIOs teamed up with other IT stakeholders in the insurance industry in the U.S to conduct a study that found that only 18% of COBOL to C# modernization projects complete within the scheduled period. Further research revealed that poor legacy application understanding was the primary reason projects could not end as expected.
Furthermore, using the accuracy of the legacy system for planning and poor understanding of the breadth of the influence of the company rules and policies within the legacy system are some of the risks associated with migrating from COBOL to C# solutions. The way an organization understands the source environment could also impact the ability to plan and implement a modernization project successfully. However, accurate, in-depth knowledge about the source environment can help reduce the chances of cost overrun since workers understand the internal operations in the migration project. That way, companies can understand how time and scope impact the efforts required to implement a plan successfully.
Use of Sequential Files
Companies often use sequential files as an intermediary when migrating from COBOL to C# solution to save data. Alternatively, sequential files can be used for report generation or communication with other programs. However, software mining doesn’t migrate these files to SQL tables; instead, it maintains them on file systems. Companies can use data generated on the COBOL system to continue to communicate with the rest of the system at no risk. Sequential files also facilitate a secure migration path to advanced standards such as MS Excel.
Modern systems offer companies a range of portfolio analysis that allows for narrowing down their scope of legacy application migration. Organizations may also capitalize on it to shed light on migration rules hidden in the ancient legacy environment. COBOL to C# modernization solution uses an extensible and fully maintainable code base to develop functional equivalent target application. Migration from COBOL solution to C# applications involves language translation, analysis of all artifacts required for modernization, system acceptance testing, and database and data transfer. While it’s optional, companies could need improvements such as coding improvements, SOA integration, clean up, screen redesign, and cloud deployment.
Tech Life in Wyoming
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Wyoming since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about IBM programming
- Get your questions answered by easy to follow, organized IBM experts
- Get up to speed with vital IBM programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
