Google for Business Training Classes in Olympia, Washington
Learn Google for Business in Olympia, Washington and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Google for Business related training offerings in Olympia, Washington: Google for Business Training
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Evolving technologies become fun due to the immense advantages and features they bring with them. Fighting change though is human and while we may initially resist such changes, it is always better to accept them to our advantage.
Switching to HTML 5 is one such change we need to be ready for and there are at least 8 reasons why we should be doing so which are explained later in the article.
Earlier HTML was mainly used only for Web content development. But with the arrival of HTML 5, there would be a radical shift in that it would be used more and more for the development of many of the client side applications as well. The advantages straight away are that CSS as well as JavaScript become free due to the open architecture environment. HTML 5 is also pretty light and has a much easier code to read, making it convenient for devices like smart phones and tablets running on batteries to use the applications.
The 8 reasons mentioned above are as under:
As developers we are overwhelmed with the number of language choices made available to us. It wasn't so long ago that C and it's object oriented sibling C++ where the mainstay of any programmer. Now though we have languages which make certain tasks so easy and simple that we simply cannot afford to ignore them.
In this article we are going to look at the overall differences between Python, Perl and TCL. All formidable and worthy in their own right, but each one has been designed to suit a specific programming need.
1)– Perl is the most mature out of the three languages we are looking at in this article. It was originally designed for processing textual data, and it does so extremely well. Of course Perl has grown over time and can be used for a multitude of different programming scenarios.
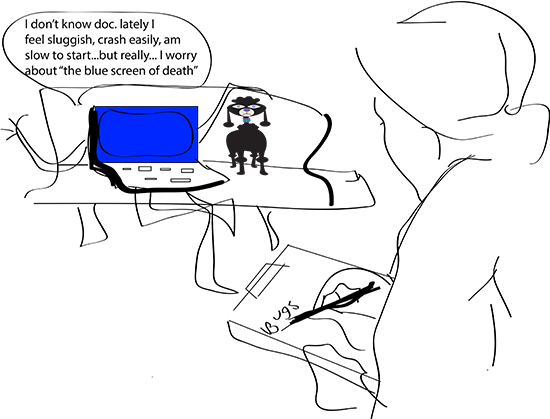 Technology is wonderful. It helps us run our businesses and connects us to the world. But when computer problems get in the way of getting what you need to get done, you can go from easygoing to mad-as-a-hornet in 3 seconds flat. Before you panic or give in to the temptation to throw your computer out the window, try these easy fixes.
Technology is wonderful. It helps us run our businesses and connects us to the world. But when computer problems get in the way of getting what you need to get done, you can go from easygoing to mad-as-a-hornet in 3 seconds flat. Before you panic or give in to the temptation to throw your computer out the window, try these easy fixes.
5 Common Computer Problems
- Sluggish PC
A sluggish PC often means low disk space caused by an accumulation of temporary Internet files, photos, music, and downloads. One of the easiest fixes for a slow PC is to clear your cache.
The way you’ll do this will depend on the Internet browser you use:
- Chrome– On the top right-hand side of the screen, you’ll see what looks like a window blind. Click on that. Click on ‘History’ and hit ‘Clear Browsing Data’.
- Safari– On the upper left-hand side, you’ll see a tab marked ‘Safari’. Click on that. Scroll down and hit ‘Empty Cache’.
- Internet Explorer– Click on ‘Tools’ and scroll down to ‘Internet Options’. Under ‘Browsing History’ click ‘Delete’. Delete files and cookies.
- FireFox – At the top of the window click ‘Tools’ then go to ‘Options’. Select the ‘Advanced’ panel and click on the ‘Network’ tab. Go to ‘Cached Web Content’ and hit ‘Clear Now’.
We are not all equally motivated. Some people have more self-drive than other people. This is why we find that some people always end up at the top even when the odds are against them. An employee, with this realization, through the Human Resource department, should be able to design efficient career development systems. For this system to work, the employer must understand the nature of the business environment in which they are operating.
Why Train Employees?
The purpose of training employees is to enable them to grow with time and increase their efficiency. The business world is quite dynamic, nothing stays the same for long. Training one’s employees allows them to keep abreast with the ever changing technological advancements and many other factors that are relevant to his/her line of work. Employees cannot be expected to solve all their employer’s expectations with static skills and techniques. Even the most updated technology becomes obsolete at some point.
People are the biggest assets in organizations. For an establishment to flourish, it is important that the employer understands certain key things that help spur their development.
In a report from the Harvard Business Review, “The Impact of Employee Engagement of Performance,” the most impactful employee drivers are:
Tech Life in Washington
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Symetra Financial Corporation | Bellevue | Financial Services | Insurance and Risk Management |
| Alaska Air Group, Inc. | Seattle | Travel, Recreation and Leisure | Passenger Airlines |
| Expedia, Inc. | Bellevue | Travel, Recreation and Leisure | Travel Agents & Services |
| Itron, Inc. | Liberty Lake | Computers and Electronics | Instruments and Controls |
| PACCAR Inc. | Bellevue | Manufacturing | Automobiles, Boats and Motor Vehicles |
| Puget Sound Energy Inc | Bellevue | Energy and Utilities | Gas and Electric Utilities |
| Expeditors International of Washington, Inc. | Seattle | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Costco Wholesale Corporation | Issaquah | Retail | Grocery and Specialty Food Stores |
| Starbucks Corporation | Seattle | Retail | Restaurants and Bars |
| Nordstrom, Inc. | Seattle | Retail | Department Stores |
| Weyerhaeuser Company | Federal Way | Manufacturing | Paper and Paper Products |
| Microsoft Corporation | Redmond | Software and Internet | Software |
| Amazon.com, Inc. | Seattle | Retail | Sporting Goods, Hobby, Book, and Music Stores |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Washington since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Google for Business programming
- Get your questions answered by easy to follow, organized Google for Business experts
- Get up to speed with vital Google for Business programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
