Tcl, Awk, Bash, Shell Training Classes in Missoula, Montana
Learn Tcl, Awk, Bash, Shell in Missoula, Montana and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Tcl, Awk, Bash, Shell related training offerings in Missoula, Montana: Tcl, Awk, Bash, Shell Training
Tcl, Awk, Bash, Shell Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
Blog Entries publications that: entertain, make you think, offer insight
 The mainstay of a corporation is the data that it possesses. By data, I mean its customer base, information about the use of its products, employee roles and responsibilities, the development and maintenance of its product lines, demographics of supporters and naysayers, financial records, projected sales ... It is in the organization of this data that advancements to the bottom line are often realized i.e. the nuggets of gold are found. Defining what is important, properly cataloging the information, developing a comprehensive protocol to access and update this information and discerning how this data fits into the corporate venacular is basis of this data organization and may be the difference between moving ahead of the competition or being the one to fall behind.
The mainstay of a corporation is the data that it possesses. By data, I mean its customer base, information about the use of its products, employee roles and responsibilities, the development and maintenance of its product lines, demographics of supporters and naysayers, financial records, projected sales ... It is in the organization of this data that advancements to the bottom line are often realized i.e. the nuggets of gold are found. Defining what is important, properly cataloging the information, developing a comprehensive protocol to access and update this information and discerning how this data fits into the corporate venacular is basis of this data organization and may be the difference between moving ahead of the competition or being the one to fall behind.
Whenever we attempt to develop an Enterprise Rule Application, we must begin by harvesting the data upon which those rules are built. This is by no means an easy feat as it requires a thorough understanding of the business, industry, the players and their respective roles and the intent of the application. Depending upon the scope of this undertaking, it is almost always safe to say that no one individual is completely knowledgeable to all facets needed to comprise the entire application.
The intial stage of this endeavor is, obviously, to decide upon the intent of the application. This requires knowledge of what is essential, what is an add-on and which of all these requirements/options can be successfully implemented in the allotted period of time. The importance of this stage cannot be stressed enough; if the vision/goal cannot be articulated in a manner that all can understand, the knowledge tap will be opened to become the money drain. Different departments may compete for the same financial resources; management may be jockeying for their day in the sun; consulting corporations, eager to win the bid, may exaggerate their level of competency. These types of endeavors require those special skills of an individual or a team of very competent members to be/have a software architect, subject matter expert and business analyst.
Once the decision has been made and the application development stages have been defined, the next step is to determine which software development tools to employ. For the sake of this article, we will assume that the team has chosen an object oriented language such as Java and a variety of J EE components, a relationsional database and a vendor specific BRMS such as Blaze Advisor. Now, onto the point of this article.
Information Technology is one of the most dynamic industries with new technologies surfacing frequently. In such a scenario, it can get intimidating for information technology professionals at all levels to keep abreast of the latest technology innovations worth investing time and resources into.
It can therefore get daunting for entry and mid-level IT professionals to decide which technologies they should potentially be developing skills. However, the biggest challenge comes for senior information technology professionals responsible for driving the IT strategy in their organizations.
It is therefore important to keep abreast of the latest technology trends and get them from reputable sources. Here are some of the ways to keep on top of the latest trends in Information Technology.
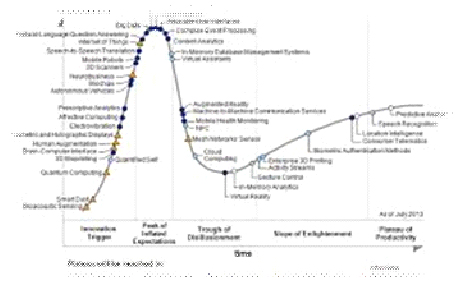
· Subscribe to leading Analyst Firms: If you work for a leading IT organization, chances are that you already have subscription to leading IT analyst firms notably Gartner and Forrester. These two firms are some of the most recognized analyst firms with extensive coverage on almost every enterprise technology including hardware and software. These Analyst firms frequently publish reports on global IT spending and trends that are based on primary research conducted on vendors and global CIOs & CTOs. However, subscription to these reports is very expensive and if you are a part of a small organization you may have issues securing access to these reports. One of the most important pieces of research published by these firms happens to be the Gartner Hype Cycle which plots leading technologies and their maturity curve.Even if you do not have access to Gartner research, you can hack your way by searching for “Gartner Hype Cycle” on Google Images and you will in most cases be able to see the plots similar to the one below
Back in the late 90's, there were a number of computer scienctists claiming to know java in hopes of landing a job for $80k+/year. In fact, I know a woman you did just that: land a project management position with a large telecom and have no experience whatsoever. I guess the company figured that some talent was better than no talent and that, with some time and training, she would be productive. Like all gravey train stories, that one, too, had an end. After only a year, she was given a pink slip.
Not only are those days over, job prospects for the IT professional have become considerably more demanding. Saying you know java today is like saying you know that you have expertise with the computer mouse; that's nice, but what else can you do. This demand can be attributed to an increase in global competition along with the introduction of a number of varied technologies. Take .NET, Python, Ruby, Spring, Hibernate ... as an example; most of them, along with many others, are the backbone of the IT infrastructure of most mid-to-large scale US corporations. Imagine the difficulty in finding the right mix of experience, knowledge and talent to support, maintain and devlop with such desparate technologies.
Well imagine no more. According to the IT Hiring Index and Skills Report, seventy percent of CIO’s said it's challenging to find skilled professionals today. If we add the rapid rate of technological innovation into the mix of factors affecting more businesses now than ever before, it’s understandable that the skill gap is widening. Consider this as well: the economic downturn has forced many potential retires to remain in the workforce. This is detailed in MetLife's annual Study of Employee Benefits which states that“more than one-third of surveyed Baby Boomers (35%) say that as a result of economic conditions they plan to postpone their retirement.” How then does the corporation hire new, more informed/better educated talent? Indeed, the IT skills gap is ever widening.
In order to compensate for these skill discrepencies, many firms have resorted to hire the ideal candidates by demanding they possess a christmas wish list of expertise in a variety of different IT disciplines. It would not be uncommon that such individuals have a strong programming background and are brilliant DBA's. What about training? That is certainly a way to diminish the skills gap.
I’ll get straight to the point. Why should companies invest more in management training? Here are 10 simple reasons.
1) An employee’s relationship with his or her direct manager is the most important single factor in employee engagement.
2) Engaged employees are happier and more productive. Disengaged employees are frustrated and more disruptive.
3) Because there’s no widely agreed-on skillset for management (good managers come in all shapes and sizes), there’s an assumption everyone knows how to do it. This is akin to someone who’s never driven before being given keys to a car and told: “Drive.” (Many many years ago, this is how I first learned to manage. I blundered my way through it. Trial and error. It wasn’t pretty.)
Tech Life in Montana
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Montana since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Tcl, Awk, Bash, Shell programming
- Get your questions answered by easy to follow, organized Tcl, Awk, Bash, Shell experts
- Get up to speed with vital Tcl, Awk, Bash, Shell programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…