C# Programming Training Classes in Syracuse, New York
Learn C# Programming in Syracuse, NewYork and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current C# Programming related training offerings in Syracuse, New York: C# Programming Training
C# Programming Training Catalog
subcategories
Microsoft Development Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Ruby Programming
29 April, 2024 - 1 May, 2024 - Go Language Essentials
29 July, 2024 - 1 August, 2024 - VMware vSphere 8.0 with ESXi and vCenter
10 June, 2024 - 14 June, 2024 - RED HAT ENTERPRISE LINUX V7 DIFFERENCES
13 May, 2024 - 15 May, 2024 - VMware vSphere 8.0 Boot Camp
10 June, 2024 - 14 June, 2024 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Smart Project Management –Best Practices of Good Managers
Project management could be one of the easiest jobs on the planet, and could also be the worst nightmare. The difference between the two extremes depends on smart management of a project. According to the project management institute, there are five phases in project management - Initiating, Planning, Executing, Monitoring & Controlling, and Closing.
Every manager has his own style of project management. But there are a lot of contributing factors that result in a successfully managed project. These factors vary from project to project, but they all contain some common elements.
1. Setting SMART Goals
Information Technology is one of the most dynamic industries with new technologies surfacing frequently. In such a scenario, it can get intimidating for information technology professionals at all levels to keep abreast of the latest technology innovations worth investing time and resources into.
It can therefore get daunting for entry and mid-level IT professionals to decide which technologies they should potentially be developing skills. However, the biggest challenge comes for senior information technology professionals responsible for driving the IT strategy in their organizations.
It is therefore important to keep abreast of the latest technology trends and get them from reputable sources. Here are some of the ways to keep on top of the latest trends in Information Technology.
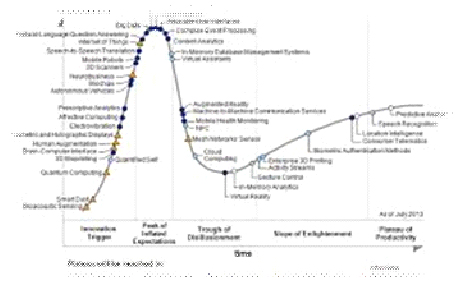
· Subscribe to leading Analyst Firms: If you work for a leading IT organization, chances are that you already have subscription to leading IT analyst firms notably Gartner and Forrester. These two firms are some of the most recognized analyst firms with extensive coverage on almost every enterprise technology including hardware and software. These Analyst firms frequently publish reports on global IT spending and trends that are based on primary research conducted on vendors and global CIOs & CTOs. However, subscription to these reports is very expensive and if you are a part of a small organization you may have issues securing access to these reports. One of the most important pieces of research published by these firms happens to be the Gartner Hype Cycle which plots leading technologies and their maturity curve.Even if you do not have access to Gartner research, you can hack your way by searching for “Gartner Hype Cycle” on Google Images and you will in most cases be able to see the plots similar to the one below
I suspect that many of you are familiar with the term "hard coding a value" whereby the age of an individual or their location is written into the condition (or action) of a business rule (in this case) as shown below:
if customer.age > 21 and customer.city == 'denver'
then ...
Such coding practices are perfectly expectable provided that the conditional values, age and city, never change. They become entirely unacceptable if a need for different values could be anticipated. A classic example of where this practice occurred that caused considerable heartache in the IT industry was the Y2K issue where dates were updated using only the last 2 digits of a four digit number because the first 2 digits were hard-coded to 19 i.e. 1998, 1999. All was well provided that the date did not advance to a time beyond the 1900’s since no one could be certain of what would happen when the millennia arrived (2000). A considerably amount of work (albeit boring) and money, approximately $200 billion, went into revising systems by way of software rewrites and computer chip replacements in order to thwart any detrimental outcomes. It is obvious how a simple change or an assumption can have sweeping consequences.
You may wonder what Y2K has to do with Business Rule Management Systems (BRMS). Well, what if we considered rules themselves to be hard-coded. If we were to write 100s of rules in Java, .NET or whatever language that only worked for a given scenario or assumption, would that not constitute hard-coded logic? By hard-coded, we obviously mean compiled. For example, if a credit card company has a variety of bonus campaigns, each with their own unique list of rules that may change within a week’s time, what would be the most effective way of writing software to deal with these responsibilities?
Viruses, trojans, and other malicious programs are everywhere. There's always a new threat to your computer's security, and many of these threats invade your computer without you even knowing. Most viruses aren't going to loudly announce themselves, so it's important to know the hidden ways in which your computer can become infected.
Infected Files from Other Computers
Whether you're borrowing someone's flash drive or grabbing a file from their computer, your computer can become infected if the file or device you're using already contains a virus, trojan, or other form of malware.
This is a very common issue, and you won't even know there's a problem most of the time. For example, if your computer is connected to other devices on a network, and you decide to pull an important file off of another computer on the network, your computer will become infected if the file you took has a virus attached to it.
Also, if you forgot your flash drive, and you need to use your friend or coworker's device for the day, then even plugging the device into your computer can cause the infection in the flash drive to be transmitted.
Downloading Legitimate Programs
Another way your computer can be secretly infected is when you download a legitimate program and run it. There are numerous legitimate programs on the internet that can help you in many ways. The programs themselves could be infected, though.
Also, one of the most common ways your computer can become infected is when you don't read the fine print before you download a program. Some of them may insist that you install another small program in addition to the one you initially chose. The boxes that you are supposed to click to give your consent may already be clicked.
This small extra program is the one that may carry an infection that will spread to your computer when you run the main program. You may get a lot of good use out of the legitimate program, but the virus attached to the extra hidden program can cause you a lot of trouble.
Using Vulnerable Applications
Security is a serious matter. If even one of the applications you use on your computer is vulnerable to becoming hacked or infected, then your entire computer is at risk and could become secretly infected. Anything from PDF viewing applications to your operating system can become infected if you don't download the latest security patches and keep everything up-to-date.
Not Using Antivirus Software
Antivirus software can protect your computer from a number of viruses, trojans, and other problems. Your computer can become infected in a number of ways, so you need to have good antivirus software to provide strong protection from hidden attacks.
Viruses, trojans, and other malware can infect your computer in a variety of hidden ways. To prevent infection and problems, you need to be careful about what you download, and you should keep your applications secure. Also, find reliable antivirus software to help.
Related:
How Do IT Placement Agencies Work?
5 Disruptive Technologies for the Enterprise: What are the Implications?
Tech Life in New York
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| NYSE Euronext, Inc. | New York | Financial Services | Securities Agents and Brokers |
| Anderson Instrument Company Inc. | Fultonville | Manufacturing | Tools, Hardware and Light Machinery |
| News Corporation | New York | Media and Entertainment | Radio and Television Broadcasting |
| Philip Morris International Inc | New York | Manufacturing | Manufacturing Other |
| Loews Corporation | New York | Travel, Recreation and Leisure | Hotels, Motels and Lodging |
| The Guardian Life Insurance Company of America | New York | Financial Services | Insurance and Risk Management |
| Jarden Corporation | Rye | Manufacturing | Manufacturing Other |
| Ralph Lauren Corporation | New York | Retail | Clothing and Shoes Stores |
| Icahn Enterprises, LP | New York | Financial Services | Investment Banking and Venture Capital |
| Viacom Inc. | New York | Media and Entertainment | Media and Entertainment Other |
| Omnicom Group Inc. | New York | Business Services | Advertising, Marketing and PR |
| Henry Schein, Inc. | Melville | Healthcare, Pharmaceuticals and Biotech | Medical Supplies and Equipment |
| Pfizer Incorporated | New York | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| Eastman Kodak Company | Rochester | Computers and Electronics | Audio, Video and Photography |
| Assurant Inc. | New York | Business Services | Data and Records Management |
| PepsiCo, Inc. | Purchase | Manufacturing | Nonalcoholic Beverages |
| Foot Locker, Inc. | New York | Retail | Department Stores |
| Barnes and Noble, Inc. | New York | Retail | Sporting Goods, Hobby, Book, and Music Stores |
| Alcoa | New York | Manufacturing | Metals Manufacturing |
| The Estee Lauder Companies Inc. | New York | Healthcare, Pharmaceuticals and Biotech | Personal Health Care Products |
| Avon Products, Inc. | New York | Healthcare, Pharmaceuticals and Biotech | Personal Health Care Products |
| The Bank of New York Mellon Corporation | New York | Financial Services | Banks |
| Marsh and McLennan Companies | New York | Financial Services | Insurance and Risk Management |
| Corning Incorporated | Corning | Manufacturing | Concrete, Glass, and Building Materials |
| CBS Corporation | New York | Media and Entertainment | Radio and Television Broadcasting |
| Bristol Myers Squibb Company | New York | Healthcare, Pharmaceuticals and Biotech | Biotechnology |
| Citigroup Incorporated | New York | Financial Services | Banks |
| Goldman Sachs | New York | Financial Services | Personal Financial Planning and Private Banking |
| American International Group (AIG) | New York | Financial Services | Insurance and Risk Management |
| Interpublic Group of Companies, Inc. | New York | Business Services | Advertising, Marketing and PR |
| BlackRock, Inc. | New York | Financial Services | Securities Agents and Brokers |
| MetLife Inc. | New York | Financial Services | Insurance and Risk Management |
| Consolidated Edison Company Of New York, Inc. | New York | Energy and Utilities | Gas and Electric Utilities |
| Time Warner Cable | New York | Telecommunications | Cable Television Providers |
| Morgan Stanley | New York | Financial Services | Investment Banking and Venture Capital |
| American Express Company | New York | Financial Services | Credit Cards and Related Services |
| International Business Machines Corporation | Armonk | Computers and Electronics | Computers, Parts and Repair |
| TIAA-CREF | New York | Financial Services | Securities Agents and Brokers |
| JPMorgan Chase and Co. | New York | Financial Services | Investment Banking and Venture Capital |
| The McGraw-Hill Companies, Inc. | New York | Media and Entertainment | Newspapers, Books and Periodicals |
| L-3 Communications Inc. | New York | Manufacturing | Aerospace and Defense |
| Colgate-Palmolive Company | New York | Consumer Services | Personal Care |
| New York Life Insurance Company | New York | Financial Services | Insurance and Risk Management |
| Time Warner Inc. | New York | Media and Entertainment | Media and Entertainment Other |
| Cablevision Systems Corp. | Bethpage | Media and Entertainment | Radio and Television Broadcasting |
| CA Technologies, Inc. | Islandia | Software and Internet | Software |
| Verizon Communications Inc. | New York | Telecommunications | Telephone Service Providers and Carriers |
| Hess Corporation | New York | Energy and Utilities | Gasoline and Oil Refineries |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in New York since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about C# Programming programming
- Get your questions answered by easy to follow, organized C# Programming experts
- Get up to speed with vital C# Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…