Perl Programming Training Classes in North Little Rock, Arkansas
Learn Perl Programming in North Little Rock, Arkansas and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Perl Programming related training offerings in North Little Rock, Arkansas: Perl Programming Training
Perl Programming Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
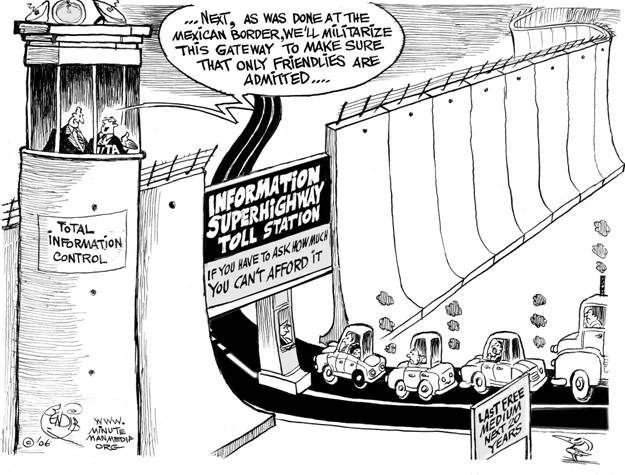
Net Neutrality
You may have heard about net neutrality over the years. Recently, the concept has gone through some changes, and many would consider its underlying principles to be in danger of corruption or dissolution. However, the technical nature of net neutrality ethics makes it difficult to understand for the layperson. Read on, and the central themes and controversies surrounding the principle will be outlined and explained for your convenience.
The Theme
The job market is extremely tight these days, with several qualified workers being available for each empty position. That means that should you find yourself looking for work, for whatever reason, you need to make sure your interview skills are up to snuff. We will be taking a look at a variety of different tips that will help ensure your success during the interview process, including how to make sure your employers know about your C training experience. Here are some others:
- Do your own research in advance – Before you even step through the doorway to initiate the application process with a company, you should already know quite a bit about it. Investigate the corporate culture, speak with contacts who have experience with the firm, or search online; however you do it, having as much information as possible can really help you get an advantage during the hiring process. If you have specific experience, such as C training, that is of exceptional value to the firm you are applying to you can market yourself more effectively to the hiring agent.
- Dress Appropriately – In a perfect world, programming skill and experience such as C training should be the only factors in consideration when looking at a prospective hire; in real life this is often not the case. Don’t miss out because you gave a bad impression to someone, and strive to look your absolute best during your job interview. It is unfortunate, but the IT industry in particular tends to have a reputation for lacking in this department, so breaking the mold can be of great benefit to you.
- Be ready to interview at all times – You may be surprised how often job candidates are asked to participate in an off-the-cuff phone interview on the spot. Same-day in person interviews also are rising in popularity. Make sure you are always able to respond quickly if these situations come up and you get a fast interview. Memorize a few points in advance you can use to pump yourself up, such as an anecdote about your C training or other particular skills you may possess.
Job interviews are notoriously stressful for many people. Using simple tips like these can help you to prepare in advance for situations you may encounter during the interview process, and help you ultimately secure that new job. Make sure to emphasize whatever makes you special as an individual, such as your extensive C training.
The iconic software company that is based in King County Washington has been getting almost universally slammed from it's recent Los Angeles press announcement about its entry into the hardware business with the convertible laptop/tablet known as Surface.
Certainly I can see the point that it is now competing with its hardware vendors/partners. Intel has done a good job in the arena creating 'reference designs' without competing with its partners.
There is another viewpoint which seems to be ignored. The cold facts are Microsoft is a public company. This puts Microsoft in a legal position of doing the most it can to return value to its shareholders. Failure to do so means somebody is going to jail.
Microsoft has a vision, which at the end of the day is, a certain way to get enough people to see enough value to hand over their money, to fulfill their fiduciary duty.
Last year, Hewlett-Packard purchased Autonomy for $10 billion, enduring a number of arrows from its competitor Oracle. What a difference a year is!
Since the purchase HP saw the leaving of Autonomy CEO Mike Lynch, which was not on friendly terms. It also saw the departure of the whole original management team and 20 percent of the staff. Now, the question is whether or not HP will see its move compensate or become another WebOS-style fiasco, marking the company needs to stay with hardware.
Tech Life in Arkansas
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Murphy Oil Corporation | El Dorado | Energy and Utilities | Gasoline and Oil Refineries |
| J.B. Hunt Transport Services, Incorporated | Lowell | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Tyson Foods, Inc. | Springdale | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| Dillard's, Inc. | Little Rock | Retail | Department Stores |
| Wal-Mart Stores, Inc | Bentonville | Retail | Department Stores |
| Windstream Corporation | Little Rock | Telecommunications | Telephone Service Providers and Carriers |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Arkansas since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Perl Programming programming
- Get your questions answered by easy to follow, organized Perl Programming experts
- Get up to speed with vital Perl Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
