Python Programming Training Classes in St. Louis, Missouri
Training Suggestions from the Experts

An Experienced Python developer must have
... an understanding of the following topics: Map, Reduce and Filter, Numpy, Pandas, MatplotLib, File handling and Database integration. All of these requirements assume a solid grasp of Python Idioms that include iterators, enumerators, generators and list comprehensions.
To quickly get up to speed, we suggest you enroll in the following classes: Beginning Python and Advanced Python 3
Call for Details: 303.377.6176
Learn Python Programming in St. Louis, Missouri and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Python Programming related training offerings in St. Louis, Missouri: Python Programming Training
Python Programming Training Catalog
subcategories
Web Development Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Information Technology is one of the most dynamic industries with new technologies surfacing frequently. In such a scenario, it can get intimidating for information technology professionals at all levels to keep abreast of the latest technology innovations worth investing time and resources into.
It can therefore get daunting for entry and mid-level IT professionals to decide which technologies they should potentially be developing skills. However, the biggest challenge comes for senior information technology professionals responsible for driving the IT strategy in their organizations.
It is therefore important to keep abreast of the latest technology trends and get them from reputable sources. Here are some of the ways to keep on top of the latest trends in Information Technology.
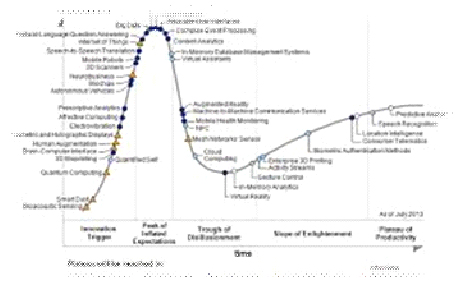
· Subscribe to leading Analyst Firms: If you work for a leading IT organization, chances are that you already have subscription to leading IT analyst firms notably Gartner and Forrester. These two firms are some of the most recognized analyst firms with extensive coverage on almost every enterprise technology including hardware and software. These Analyst firms frequently publish reports on global IT spending and trends that are based on primary research conducted on vendors and global CIOs & CTOs. However, subscription to these reports is very expensive and if you are a part of a small organization you may have issues securing access to these reports. One of the most important pieces of research published by these firms happens to be the Gartner Hype Cycle which plots leading technologies and their maturity curve.Even if you do not have access to Gartner research, you can hack your way by searching for “Gartner Hype Cycle” on Google Images and you will in most cases be able to see the plots similar to the one below
 Much of success is about performance. It’s about what we do and what we are able to inspire others to do. There are some simple performance principles I have learned in my life, and I want to share them with you. They really bring success, and what it takes to be successful, into sharp focus. They are also the basis for developing and maintaining an expectation of success.
Much of success is about performance. It’s about what we do and what we are able to inspire others to do. There are some simple performance principles I have learned in my life, and I want to share them with you. They really bring success, and what it takes to be successful, into sharp focus. They are also the basis for developing and maintaining an expectation of success.
The Five Principles of Performance
1. We generally get from ourselves and others what we expect. It is a huge fact that you will either live up or down to your own expectations. If you expect to lose, you will. If you expect to be average, you will be average. If you expect to feel bad, you probably will. If you expect to feel great, nothing will slow you down. And what is true for you is true for others. Your expectations for others will become what they deliver and achieve. As Gandhi said, “Be the change you wish to see in the world.”
2. The difference between good and excellent companies is training. The only thing worse than training employees and losing them is to not train them and keep them! A football team would not be very successful if they did not train, practice, and prepare for their opponents. When you think of training as practice and preparation, it makes you wonder how businesses survive that do not make significant training investments in their people.
Actually, companies that do not train their people and invest in their ability don’t last. They operate from a competitive disadvantage and are eventually gobbled up and defeated in the marketplace. If you want to improve and move from good to excellent, a good training strategy will be the key to success.
Due to the advancements in technology, teens and adults alike can now partake in virtual worlds thanks to video games. Video games are enjoyed as a hobby all over the globe, but some gamers have made it their career with help from the ever-growing e-sport community. This is an inside look at the professional level of gaming from an ex-MLG participant, and what I remember going through when starting to play video games at an elite level.
One of the premiere and most popular leagues within the United States happens to be Major League Gaming or MLG for short. This is a league that usually involves more of the most recent games out, and they create circuits for each major title and its subsequent releases. Two of the most major game circuits within the MLG league were the Halo series and the Call of Duty series, both which happened to be first person shooters (FPS). There were a potential hundred or so teams within each circuit, but much like other competitions, the circuits were ran with winner’s brackets and losers brackets. This means that out of all the teams that would show up to MLG events, about the top eight of each bracket would really be known as the "elite" players. I personally played in the Gears of War circuit at venues like MLG Raleigh and MLG Toronto, and we had very few teams compared to Call of Duty and Halo. The amount of participants at each event usually varies in each circuit based on the popularity of the game being played.
When you win tournaments, the payouts are split between the team members. This means that looking at playing in the MLG for a life career is an ill-advised move. The cost to get to events and buy team passes usually negates the prizes you win most of the time, considering by the time that the prize money is split you are left with about $800 in a popular circuit (Like Call of Duty). The payouts are usually only high in special and certain occasions, one for example being the million dollar showdown that Infinity Ward hosted for Call of Duty: Modern Warfare 3 a couple years back. The way that players that make professional gaming their career get the big money now is by being sponsored by the big companies that back the league like Red Bull and Hot Pockets. MLG players like "Walshy" and "FeaR Moho" were sponsored early on in the league and were able to make a living off of the games they played. I would imagine them getting around $60K in a good year off of sponsors alone. I would go even as far as to say that if you do not have a sponsor in e-sports, you will not be financially successful in the career.
Being an MLG gamer requires passion and understanding for the games. If you just want to make money, then you are better off working at McDonalds.
How to Keep a Start Up Team Motivated?
What People Should Know Before Getting Rid of Old Tech Stuff
Surprising Ways Viruses, Malware, Etc. are Infecting Computers
Python programming language is general purpose open source programming language. One of its main features is flexibility and ease of use. Python has a variety of useful set of utilities and libraries for data processing and analytical tasks. Currently due to the rise in demand of big data processing python has grown in popularity because its features are easy to use which are core to the processing of huge chunks of information.
Guido Van Rossum, the pioneer of python, introduced python in the year 1980 and then implemented it in 1989. The intention behind the development of python was to make it open source language that can also be used for commercial projects. The fundamental principle of python is to write the code that is easy to use, highly readable and embrace writing fewer lines of code for achieving a particular task. One of the most popular standard libraries which have ready to use tools for performing a various work is Python Package Index. It was introduced in January 2016 and contains more than 72,000 packages for third-party software usage.
Python plays a critical role in linking data to customers. Recently python has found few entry barriers and many people have had access to have experienced the power of python in the past. So, what makes python the best language for big data analytics?
One of the reasons to choose python is that python ecosystem is very vibrant, the ratings at Redmonk are a proof of the strength python community. The Redmonk ranking is based on StackOverflow discussions and contribution made in Github to determine the popularity of programming language on the method used by users to ask questions about Python and the number of the open source projects contributions.
Tech Life in Missouri
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Patriot Coal Corporation | Saint Louis | Agriculture and Mining | Mining and Quarrying |
| Solutia Inc. | Saint Louis | Manufacturing | Chemicals and Petrochemicals |
| Monsanto Company | Saint Louis | Agriculture and Mining | Agriculture and Mining Other |
| Kansas City Power and Light Company | Kansas City | Energy and Utilities | Gas and Electric Utilities |
| The Laclede Group, Inc. | Saint Louis | Energy and Utilities | Gas and Electric Utilities |
| Peabody Energy Corporation | Saint Louis | Agriculture and Mining | Mining and Quarrying |
| Emerson Electric Company | Saint Louis | Manufacturing | Tools, Hardware and Light Machinery |
| Energizer Holdings, Inc. | Saint Louis | Manufacturing | Manufacturing Other |
| Centene Corporation | Saint Louis | Healthcare, Pharmaceuticals and Biotech | Healthcare, Pharmaceuticals, and Biotech Other |
| Express Scripts | Saint Louis | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| Reinsurance Group of America, Incorporated | Chesterfield | Financial Services | Insurance and Risk Management |
| Ameren Corporation | Saint Louis | Energy and Utilities | Gas and Electric Utilities |
| DST Systems, Inc. | Kansas City | Computers and Electronics | Networking Equipment and Systems |
| Inergy, L.P. | Kansas City | Energy and Utilities | Alternative Energy Sources |
| Leggett and Platt, Incorporated | Carthage | Manufacturing | Furniture Manufacturing |
| Cerner Corporation | Kansas City | Software and Internet | Software |
| O'Reilly Automotive, Inc. | Springfield | Retail | Automobile Parts Stores |
| AMC Theatres | Kansas City | Media and Entertainment | Motion Picture Exhibitors |
| Sigma-Aldrich Corporation | Saint Louis | Manufacturing | Chemicals and Petrochemicals |
| HandR Block | Kansas City | Financial Services | Securities Agents and Brokers |
| Graybar Services, Inc. | Saint Louis | Wholesale and Distribution | Wholesale and Distribution Other |
| Edward Jones | Saint Louis | Financial Services | Personal Financial Planning and Private Banking |
| Arch Coal, Inc. | Saint Louis | Energy and Utilities | Alternative Energy Sources |
| Brown Shoe Company, Inc. | Saint Louis | Retail | Clothing and Shoes Stores |
| Ralcorp Holdings, Inc. | Saint Louis | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Missouri since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Python Programming programming
- Get your questions answered by easy to follow, organized Python Programming experts
- Get up to speed with vital Python Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
