SOA Training Classes in San Marcos, California
Learn SOA in San Marcos, California and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current SOA related training offerings in San Marcos, California: SOA Training
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
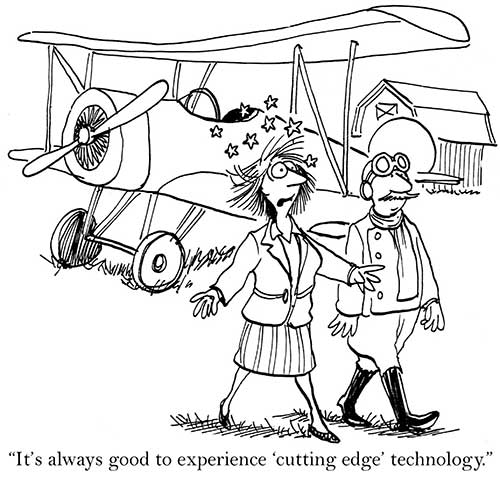
Blog Entries publications that: entertain, make you think, offer insight
As part of our Java Tutorial series, listed here are all the files you need in order to create a java socket message application.
Getting involved with the IT, or Internet Technology industry, is a way for you to break into a variety of potential coveted career paths and job openings. Whether you prefer working with the back-end of programming or if you enjoy improve user experience while browsing online, there are many different in-demand IT skills that are useful to obtain today if you are seeking a career in the tech industry yourself.
Cloud Computing
Working with cloud computing, otherwise known as "the cloud", requires you to work within various types of servers that store and access data globally from any location. With the increase in mobile usage, cloud computing is becoming even more prevalent in today's society. When you want to work with cloud computing, understanding the basics of programming and network security is a must. Working in cloud computing is a way to help with building new applications, expanding companies online as well as allowing anyone internationally to locate and access a specific blog, website or mobile app.
UX Design
UX Design is also known as user experience design. A user experience designer specializes in understanding the usability and overall experience a web visitor has when browsing on a site or blog. UX design is essential to ensure that all visitors on a website are capable of navigating the blog properly and accessing the site's content with ease, regardless of the browser they are using or the type of device that is being used to access the site itself. Cross-browser compatibility and ensuring that all websites you are working with are accessible via mobile platforms is another responsibility of many UX designers today. Working in UX design is highly recommended if you believe you have an eye for "good" web design and if you have an interest in improving the overall experience web users for a specific audience have when visiting the blog or website you represent or that you are building for yourself.
IT Security
IT security is one of the fastest-growing positions throughout the entire IT industry and field. IT security requires you to understand network infrastructures as well as how to properly manage each server individually to provide security and protection from potential hackers and online thieves looking to steal sensitive data and information. Maintaining the security of a network and all servers for a company is only becoming more popular with the expansion of mobile phone usage along with the growth of the Internet altogether.
Understanding the variety of IT skills that are in demand today can help you to better decide on a path that is right for you. The more you understand about various IT skills, the easier it is to find a position or career in your future that is most suitable for the type of work you enjoy. Whether you are looking to develop new apps or if you are interested in managing the security of company servers, there are hundreds of positions and skills that are in demand in the IT industry today.
What are the best languages for getting into functional programming?
Disruptive technologies such as hand-held devices, cloud computing and social media are rattling the foundations upon which traditional businesses are built. Enterprise customers have grown smarter at ensuring the latest technological trends work in their favor. Everyone is trying to zero in on their core competencies by employing commodity services to run their business.
Likewise, enterprise application vendors need to zero in on their core competencies and enhance more value to the businesses of their clientele by leveraging standards-based commodity services, such as IaaS and PaaS, provided by leaders in those segments (e.g. Amazon EC2, Google Cloud Platform etc.).
What else enterprises need to do is learn to adopt new and emerging technologies such as cloud, utility and social computing to build on them to penetrate new market avenues.
New small and medium-sized entrants into the market are constantly challenging enterprises given their ability to rapidly turnaround and address the requirements of the customers in a cost-effective manner. Additionally, these new advancements also affect how enterprises create, deploy, and manage solutions and applications. If you take the example of Force.com, for instance, you find that it’s a common war zone for enterprise application vendors to furnish SME markets with their applications, with the new entrants mostly having an edge.
JAVA SCRIPT TUTORIAL – THE ESSENTIAL ELEMENTS
If you are looking to increase your proficiency in programming, it can make a lot of sense to invest some time into learning how to use JavaScript, or taking a Java Script tutorial. It is one of the most popular and powerful options available today for people to use in programming different parts of their websites. It often finds use in headers, or in interactive features displayed on pages. It allows you to execute many different functions, such as calculation, pulling data from forms, special graphical effects, customized selections, custom security protocol and password systems, and much more. Here are some essential points to keep in mind:
· Java vs. JavaScript – These two languages are not the same. Java uses completely separate files for their headers and classes, and they need compilation prior to execution. Java is used in the creation of applets for pages. JavaScript is much easier and simpler to learn than regular Java, and Java Script tutorials are often significantly more accessible for the average user.
· OOP – OOP, or object oriented programming, is a specific programming technique that simplifies complicated computer programming conceptual issues. Essentially, it lets a programmer treat whole chunks of data (defined either by users, or by the system itself), and modify or access them in specific ways. It does this by classifying different parts of the programming into Objects, Methods, and Properties, which will be discussed more in depth in the future, in other Java Script Tutorials.
Tech Life in California
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Mattel, Inc. | El Segundo | Retail | Sporting Goods, Hobby, Book, and Music Stores |
| Spectrum Group International, Inc. | Irvine | Retail | Retail Other |
| Chevron Corp | San Ramon | Energy and Utilities | Gasoline and Oil Refineries |
| Jacobs Engineering Group, Inc. | Pasadena | Real Estate and Construction | Construction and Remodeling |
| eBay Inc. | San Jose | Software and Internet | E-commerce and Internet Businesses |
| Broadcom Corporation | Irvine | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| Franklin Templeton Investments | San Mateo | Financial Services | Investment Banking and Venture Capital |
| Pacific Life Insurance Company | Newport Beach | Financial Services | Insurance and Risk Management |
| Tutor Perini Corporation | Sylmar | Real Estate and Construction | Construction and Remodeling |
| SYNNEX Corporation | Fremont | Software and Internet | Data Analytics, Management and Storage |
| Core-Mark International Inc | South San Francisco | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| Occidental Petroleum Corporation | Los Angeles | Manufacturing | Chemicals and Petrochemicals |
| Yahoo!, Inc. | Sunnyvale | Software and Internet | Software and Internet Other |
| Edison International | Rosemead | Energy and Utilities | Gas and Electric Utilities |
| Ingram Micro, Inc. | Santa Ana | Computers and Electronics | Consumer Electronics, Parts and Repair |
| Safeway, Inc. | Pleasanton | Retail | Grocery and Specialty Food Stores |
| Gilead Sciences, Inc. | San Mateo | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| AECOM Technology Corporation | Los Angeles | Real Estate and Construction | Architecture,Engineering and Design |
| Reliance Steel and Aluminum | Los Angeles | Manufacturing | Metals Manufacturing |
| Live Nation, Inc. | Beverly Hills | Media and Entertainment | Performing Arts |
| Advanced Micro Devices, Inc. | Sunnyvale | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| Pacific Gas and Electric Corp | San Francisco | Energy and Utilities | Gas and Electric Utilities |
| Electronic Arts Inc. | Redwood City | Software and Internet | Games and Gaming |
| Oracle Corporation | Redwood City | Software and Internet | Software and Internet Other |
| Symantec Corporation | Mountain View | Software and Internet | Data Analytics, Management and Storage |
| Dole Food Company, Inc. | Thousand Oaks | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| CBRE Group, Inc. | Los Angeles | Real Estate and Construction | Real Estate Investment and Development |
| First American Financial Corporation | Santa Ana | Financial Services | Financial Services Other |
| The Gap, Inc. | San Francisco | Retail | Clothing and Shoes Stores |
| Ross Stores, Inc. | Pleasanton | Retail | Clothing and Shoes Stores |
| Qualcomm Incorporated | San Diego | Telecommunications | Wireless and Mobile |
| Charles Schwab Corporation | San Francisco | Financial Services | Securities Agents and Brokers |
| Sempra Energy | San Diego | Energy and Utilities | Gas and Electric Utilities |
| Western Digital Corporation | Irvine | Computers and Electronics | Consumer Electronics, Parts and Repair |
| Health Net, Inc. | Woodland Hills | Healthcare, Pharmaceuticals and Biotech | Healthcare, Pharmaceuticals, and Biotech Other |
| Allergan, Inc. | Irvine | Healthcare, Pharmaceuticals and Biotech | Biotechnology |
| The Walt Disney Company | Burbank | Media and Entertainment | Motion Picture and Recording Producers |
| Hewlett-Packard Company | Palo Alto | Computers and Electronics | Consumer Electronics, Parts and Repair |
| URS Corporation | San Francisco | Real Estate and Construction | Architecture,Engineering and Design |
| Cisco Systems, Inc. | San Jose | Computers and Electronics | Networking Equipment and Systems |
| Wells Fargo and Company | San Francisco | Financial Services | Banks |
| Intel Corporation | Santa Clara | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| Applied Materials, Inc. | Santa Clara | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| Sanmina Corporation | San Jose | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| Agilent Technologies, Inc. | Santa Clara | Telecommunications | Telecommunications Equipment and Accessories |
| Avery Dennison Corporation | Pasadena | Manufacturing | Paper and Paper Products |
| The Clorox Company | Oakland | Manufacturing | Chemicals and Petrochemicals |
| Apple Inc. | Cupertino | Computers and Electronics | Consumer Electronics, Parts and Repair |
| Amgen Inc | Thousand Oaks | Healthcare, Pharmaceuticals and Biotech | Biotechnology |
| McKesson Corporation | San Francisco | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| DIRECTV | El Segundo | Telecommunications | Cable Television Providers |
| Visa, Inc. | San Mateo | Financial Services | Credit Cards and Related Services |
| Google, Inc. | Mountain View | Software and Internet | E-commerce and Internet Businesses |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in California since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about SOA programming
- Get your questions answered by easy to follow, organized SOA experts
- Get up to speed with vital SOA programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
