JUnit, TDD, CPTC, Web Penetration Training Classes in Wichita, Kansas
Learn JUnit, TDD, CPTC, Web Penetration in Wichita, Kansas and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current JUnit, TDD, CPTC, Web Penetration related training offerings in Wichita, Kansas: JUnit, TDD, CPTC, Web Penetration Training
JUnit, TDD, CPTC, Web Penetration Training Catalog
subcategories
Android and iPhone Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
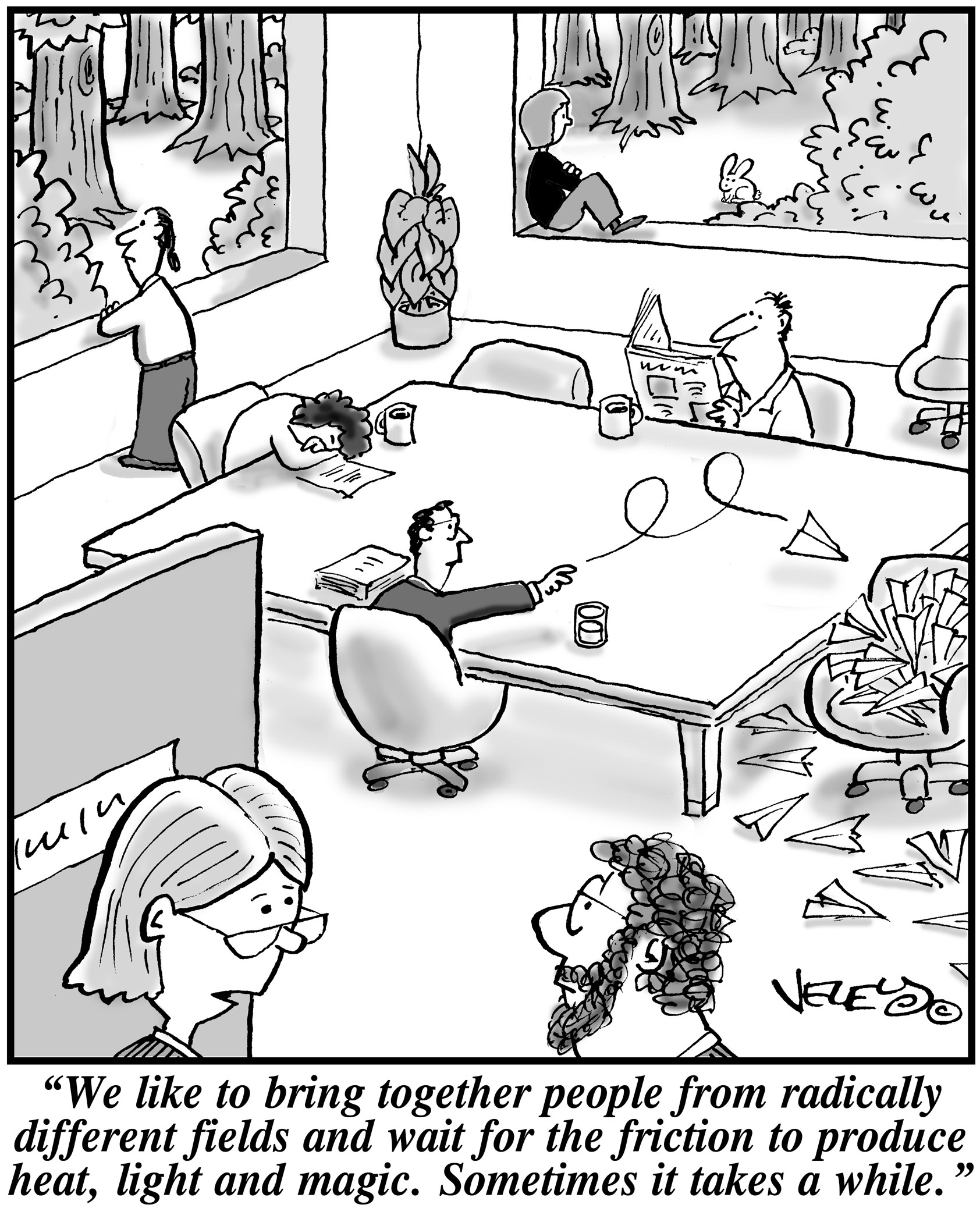 When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
The question is, what is it that great leaders like David Khasidy and Daniel Nigro do that make the difference? How do the most vulnerable companies (start ups) break the mold and become a part of our everyday lives?
It starts with their mission and vision.
Create a Strong Mission and Vision
There are many reasons why start ups fail. For one, they usually lack the capital to last through the lean times. Secondly, they often don't have the tolerance for setbacks that occur. Lastly, they do not have a long-term plan, also called a mission.
When a business has a strong mission, the team knows it and their focus toward their work and service to others within and without the company reflects that. To complement that, the shorter term vision of the company needs to be present as well.
This can even be seen in sole proprietorships with no employees, such as when Brian Pascale started his law practice. His vision was to find justice for his clients while his mission was to build upon a career that had already set precedents in the area of tort law.
As his practice has grown, new staff members can sense the vision and mission he exudes.
Encourage Ownership of Projects and Processes
Start ups need to inspire and motivate their employees because they need to know that they are not only a part of something important, but that their contributions mean something.
What won't happen if they are not there? What contribution do they make, and what are the consequences of them not fulfilling their part of the work?
By encouraging ownership in projects, team members can find that the work they are doing is not only important for the organization, but that they are going to be a big part of what makes it happen. The alternative is that they feel replaceable.
Offer Incentives That Keep the Company Competitive
When team members embrace the mission and vision of the company, and then take ownership for the company's success, they are going to need to be justly rewarded.
This could include flexible schedules (for those who don't need a stringent one), use of an account at a nearby takeout place, or even the potential for ownership as a result of a vesting program.
The incentive everyone is looking for more immediately, though, is cash. When the company takes in more revenue as a result of the efforts of those on the team, rewarding them can go a long way not only in making them feel appreciated, but in encouraging them to bring in more business.
Members of a start up team are usually very talented, and commonly underpaid. However, if they believe they are going somewhere, it will make a big difference.
Related:
Good non-programmer jobs for people with software developer experience
With an ever increasing rise in the use of employment testing, certification testing and need to get a degree, I thought I would write this basic guide on how to study for exams. Although it was originally written with the college student in mind, the fundamentals still apply to all of us in the workforce.
There are few things that strike terror into the hearts of students more than exam day, particularly if they have inadequate study skills. Perhaps these students study for hours and hours, only to discover that by exam time they've forgotten everything they've read. Below are a few study tips to help struggling students remember the information they've reviewed for their exams.
-Use memory tricks. There are a number of memory tricks that you can use to help you remember large amounts of information. For example, the use of acronyms (such as Roy G Biv to remember the colors of the rainbow) can be very helpful. In addition, you can use visualization techniques, similes, and songs to assist you in recalling your study material.
-Don't cram. Your brain requires time to absorb facts. If you know about a test in advance, start studying right away for a little bit every day, ramping up your efforts as the exam approaches.
-Take frequent breaks while studying. It may seem counter-intuitive that spending less time studying might actually help you remember more of what you've read. But taking appropriately timed study breaks will keep your mind fresh and make sure you don't stress too much.
-Write it out. For many people, writing information down as they read it is the best way to learn it. Don't just write exactly what you read, however; by rewording the information or even drawing a picture or diagram you commit it to your memory in more than one way, allowing you to remember it easier later.
-Teach it to a friend. To remember information, you have to understand it. And in order to teach information, you need to understand it as well. Nothing tests your ability to recall facts better than teaching them to another person. Find a friend unfamiliar with your study material and teach them a lesson in the subject.
-Get plenty of sleep the night before the exam. Finally, be sure to get a good night's rest the night before you take the exam. Falling asleep at your desk will accomplish nothing. This will help you be more alert while you are taking your test, and will allow you to retain more information.
 The Zen of Python, by Tim Peters has been adopted by many as a model summary manual of python's philosophy. Though these statements should be considered more as guideline and not mandatory rules, developers worldwide find the poem to be on a solid guiding ground.
The Zen of Python, by Tim Peters has been adopted by many as a model summary manual of python's philosophy. Though these statements should be considered more as guideline and not mandatory rules, developers worldwide find the poem to be on a solid guiding ground.
Beautiful is better than ugly.
Explicit is better than implicit.
Simple is better than complex.
Complex is better than complicated.
Flat is better than nested.
Sparse is better than dense.
Readability counts.
Special cases aren't special enough to break the rules.
Although practicality beats purity.
Errors should never pass silently.
Unless explicitly silenced.
In the face of ambiguity, refuse the temptation to guess.
There should be one-- and preferably only one --obvious way to do it.
Although that way may not be obvious at first unless you're Dutch.
Now is better than never.
Although never is often better than *right* now.
If the implementation is hard to explain, it's a bad idea.
If the implementation is easy to explain, it may be a good idea.
Namespaces are one honking great idea -- let's do more of those!
The original article was posted by Michael Veksler on Quora
A very well known fact is that code is written once, but it is read many times. This means that a good developer, in any language, writes understandable code. Writing understandable code is not always easy, and takes practice. The difficult part, is that you read what you have just written and it makes perfect sense to you, but a year later you curse the idiot who wrote that code, without realizing it was you.
The best way to learn how to write readable code, is to collaborate with others. Other people will spot badly written code, faster than the author. There are plenty of open source projects, which you can start working on and learn from more experienced programmers.
Readability is a tricky thing, and involves several aspects:
- Never surprise the reader of your code, even if it will be you a year from now. For example, don’t call a function max() when sometimes it returns the minimum().
- Be consistent, and use the same conventions throughout your code. Not only the same naming conventions, and the same indentation, but also the same semantics. If, for example, most of your functions return a negative value for failure and a positive for success, then avoid writing functions that return false on failure.
- Write short functions, so that they fit your screen. I hate strict rules, since there are always exceptions, but from my experience you can almost always write functions short enough to fit your screen. Throughout my carrier I had only a few cases when writing short function was either impossible, or resulted in much worse code.
- Use descriptive names, unless this is one of those standard names, such as i or it in a loop. Don’t make the name too long, on one hand, but don’t make it cryptic on the other.
- Define function names by what they do, not by what they are used for or how they are implemented. If you name functions by what they do, then code will be much more readable, and much more reusable.
- Avoid global state as much as you can. Global variables, and sometimes attributes in an object, are difficult to reason about. It is difficult to understand why such global state changes, when it does, and requires a lot of debugging.
- As Donald Knuth wrote in one of his papers: “Early optimization is the root of all evil”. Meaning, write for readability first, optimize later.
- The opposite of the previous rule: if you have an alternative which has similar readability, but lower complexity, use it. Also, if you have a polynomial alternative to your exponential algorithm (when N > 10), you should use that.
Use standard library whenever it makes your code shorter; don’t implement everything yourself. External libraries are more problematic, and are both good and bad. With external libraries, such as boost, you can save a lot of work. You should really learn boost, with the added benefit that the c++ standard gets more and more form boost. The negative with boost is that it changes over time, and code that works today may break tomorrow. Also, if you try to combine a third-party library, which uses a specific version of boost, it may break with your current version of boost. This does not happen often, but it may.
Don’t blindly use C++ standard library without understanding what it does - learn it. You look at std::vector::push_back()std::mapstd::unordered_map
Never call newdeletestd::make_uniqueusique_ptr, shared_ptr, weak_ptr
Every time you look at a new class or function, in boost or in std, ask yourself “why is it done this way and not another?”. It will help you understand trade-offs in software development, and will help you use the right tool for your job. Don’t be afraid to peek into the source of boost and the std, and try to understand how it works. It will not be easy, at first, but you will learn a lot.
Know what complexity is, and how to calculate it. Avoid exponential and cubic complexity, unless you know your N is very low, and will always stay low.
Learn data-structures and algorithms, and know them. Many people think that it is simply a wasted time, since all data-structures are implemented in standard libraries, but this is not as simple as that. By understanding data-structures, you’d find it easier to pick the right library. Also, believe it or now, after 25 years since I learned data-structures, I still use this knowledge. Half a year ago I had to implemented a hash table, since I needed fast serialization capability which the available libraries did not provide. Now I am writing some sort of interval-btree, since using std::map, for the same purpose, turned up to be very very slow, and the performance bottleneck of my code.
Notice that you can’t just find interval-btree on Wikipedia, or stack-overflow. The closest thing you can find is Interval tree, but it has some performance drawbacks. So how can you implement an interval-btree, unless you know what a btree is and what an interval-tree is? I strongly suggest, again, that you learn and remember data-structures.
These are the most important things, which will make you a better programmer. The other things will follow.
Tech Life in Kansas
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Collective Brands Inc. | Topeka | Retail | Clothing and Shoes Stores |
| Westar Energy, Inc. | Topeka | Energy and Utilities | Gas and Electric Utilities |
| Ferrellgas Partners, L.P. | Overland Park | Retail | Gasoline Stations |
| Seaboard Corporation | Shawnee Msn | Wholesale and Distribution | Grocery and Food Wholesalers |
| Sprint Corporation | Overland Park | Telecommunications | Wireless and Mobile |
| YRC WorldWide Inc. | Overland Park | Transportation and Storage | Freight Hauling (Rail and Truck) |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Kansas since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about JUnit, TDD, CPTC, Web Penetration programming
- Get your questions answered by easy to follow, organized JUnit, TDD, CPTC, Web Penetration experts
- Get up to speed with vital JUnit, TDD, CPTC, Web Penetration programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
