Azure Training Classes in Centennial, Colorado
Learn Azure in Centennial, Colorado and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Azure related training offerings in Centennial, Colorado: Azure Training
Azure Training Catalog
.NET Classes
Machine Learning Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - Linux Troubleshooting
1 June, 2026 - 5 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
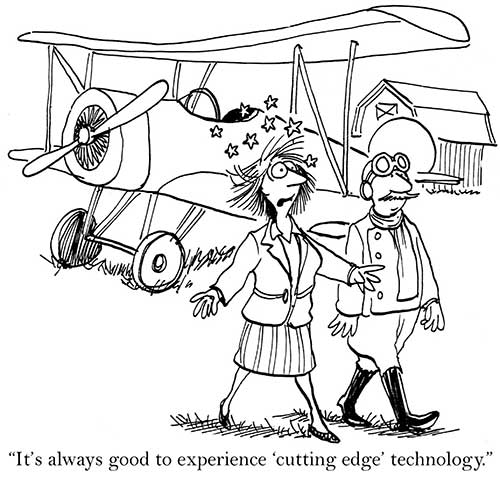
Blog Entries publications that: entertain, make you think, offer insight
Microsoft has now come up with a surface tablet to compete with the Apple iPad. The Surface is the known as the ‘iPad killer’ and ‘Microsoft iPad’. Microsoft has stuck to production of software till date but this is one of its latest hardware devices that is expected to take over the Apple iPad. This is a new challenge posed by Microsoft to Apple.
The Microsoft Surface saw its official release on 19th June in the city of Los Angeles. It has made a great first impression and seems to be beginning a new start in the competition between the best tablets in the international market. It has 10.6’’ screen and a magnetic cover that can be used as a keyboard and also as a kickstand in order to place the device upright on tables. There has been a paradigm shift in Microsoft’s policy when it decided to do away with the tile-based Metro theme for its Desktop that is almost a trademark with it.
There are many features that make the Surface more like a laptop than like a tablet- the most prominent one being the built- in keyboard that will be useful for business customers. As Microsoft Surface employs Windows 8 as an operating system, which is also used in its computers and laptops, it will be a lot easier for customers to switch among their devices.
The tablet was announced by Microsoft’s CEO, Steve Ballmer, in Los Angeles at a special press conference. It was hailed to be the first of an entirely new family of a number of devices being created and developed by the company. The Surface has a thickness of 9.3mm and weighs 1.5 pounds. It has a kickstand and keyboard for its cover. It is 0.1 mm thinner than the iPad 3, which is the latest iPad from Apple.
Today we live in the age of technology. It seems like everyone owns at least one computer, but few actually know how they work. We hear about Java tutorials and C# programming, but why are these things important?
There has been an increasing demand for those who are proficient in web development. It is a job field that has grown substantially in the past decade, and it is still continuing to flourish with no signs of stopping. Learning a web language is not only a useful skill, but a necessary one. So why, out of all of the available web languages, is Java the most valuable?
· First off, it is a simple language that is easily learned and well known.
· Java has been around for awhile now, and has earned its place as one of the pillars of modern day computer architecture. Information on Java is abundant, and ranges from online tutorials to books, such as "Java for Dummies."
Getting involved with the IT, or Internet Technology industry, is a way for you to break into a variety of potential coveted career paths and job openings. Whether you prefer working with the back-end of programming or if you enjoy improve user experience while browsing online, there are many different in-demand IT skills that are useful to obtain today if you are seeking a career in the tech industry yourself.
Cloud Computing
Working with cloud computing, otherwise known as "the cloud", requires you to work within various types of servers that store and access data globally from any location. With the increase in mobile usage, cloud computing is becoming even more prevalent in today's society. When you want to work with cloud computing, understanding the basics of programming and network security is a must. Working in cloud computing is a way to help with building new applications, expanding companies online as well as allowing anyone internationally to locate and access a specific blog, website or mobile app.
UX Design
UX Design is also known as user experience design. A user experience designer specializes in understanding the usability and overall experience a web visitor has when browsing on a site or blog. UX design is essential to ensure that all visitors on a website are capable of navigating the blog properly and accessing the site's content with ease, regardless of the browser they are using or the type of device that is being used to access the site itself. Cross-browser compatibility and ensuring that all websites you are working with are accessible via mobile platforms is another responsibility of many UX designers today. Working in UX design is highly recommended if you believe you have an eye for "good" web design and if you have an interest in improving the overall experience web users for a specific audience have when visiting the blog or website you represent or that you are building for yourself.
IT Security
IT security is one of the fastest-growing positions throughout the entire IT industry and field. IT security requires you to understand network infrastructures as well as how to properly manage each server individually to provide security and protection from potential hackers and online thieves looking to steal sensitive data and information. Maintaining the security of a network and all servers for a company is only becoming more popular with the expansion of mobile phone usage along with the growth of the Internet altogether.
Understanding the variety of IT skills that are in demand today can help you to better decide on a path that is right for you. The more you understand about various IT skills, the easier it is to find a position or career in your future that is most suitable for the type of work you enjoy. Whether you are looking to develop new apps or if you are interested in managing the security of company servers, there are hundreds of positions and skills that are in demand in the IT industry today.
What are the best languages for getting into functional programming?
Another blanket article about the pros and cons of Direct to Consumer (D2C) isn’t needed, I know. By now, we all know the rules for how this model enters a market: its disruption fights any given sector’s established sales model, a fuzzy compromise is temporarily met, and the lean innovator always wins out in the end.
That’s exactly how it played out in the music industry when Apple and record companies created a digital storefront in iTunes to usher music sales into the online era. What now appears to have been a stopgap compromise, iTunes was the standard model for 5-6 years until consumers realized there was no point in purchasing and owning digital media when internet speeds increased and they could listen to it for free through a music streaming service. In 2013, streaming models are the new music consumption standard. Netflix is nearly parallel in the film and TV world, though they’ve done a better job keeping it all under one roof. Apple mastered retail sales so well that the majority of Apple products, when bought in-person, are bought at an Apple store. That’s even more impressive when you consider how few Apple stores there are in the U.S. (253) compared to big box electronics stores that sell Apple products like Best Buy (1,100) Yet while some industries have implemented a D2C approach to great success, others haven’t even dipped a toe in the D2C pool, most notably the auto industry.
What got me thinking about this topic is the recent flurry of attention Tesla Motors has received for its D2C model. It all came to a head at the beginning of July when a petition on whitehouse.gov to allow Tesla to sell directly to consumers in all 50 states reached the 100,000 signatures required for administration comment. As you might imagine, many powerful car dealership owners armed with lobbyists have made a big stink about Elon Musk, Tesla’s CEO and Product Architect, choosing to sidestep the traditional supply chain and instead opting to sell directly to their customers through their website. These dealership owners say that they’re against the idea because they want to protect consumers, but the real motive is that they want to defend their right to exist (and who wouldn’t?). They essentially have a monopoly at their position in the sales process, and they want to keep it that way. More frightening for the dealerships is the possibility that once Tesla starts selling directly to consumers, so will the big three automakers, and they fear that would be the end of the road for their business. Interestingly enough, the big three flirted with the idea of D2C in the early 90’s before they were met with fierce backlash from dealerships. I’m sure the dealership community has no interest in mounting a fight like that again.
To say that the laws preventing Tesla from selling online are peripherally relevant would be a compliment. By and large, the laws the dealerships point to fall under the umbrella of “Franchise Laws” that were put in place at the dawn of car sales to protect franchisees against manufacturers opening their own stores and undercutting the franchise that had invested so much to sell the manufacturer’s cars. There’s certainly a need for those laws to exist, because no owner of a dealership selling Jeeps wants Chrysler to open their own dealership next door and sell them for substantially less. However, because Tesla is independently owned and isn’t currently selling their cars through any third party dealership, this law doesn’t really apply to them. Until their cars are sold through independent dealerships, they’re incapable of undercutting anyone by implementing D2C structure.
Tech Life in Colorado
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Level 3 Communications, Inc | Broomfield | Telecommunications | Telecommunications Other |
| Liberty Global, Inc. | Englewood | Telecommunications | Video and Teleconferencing |
| Liberty Media Corporation | Englewood | Media and Entertainment | Media and Entertainment Other |
| Western Union Company | Englewood | Financial Services | Financial Services Other |
| Ball Corporation | Broomfield | Manufacturing | Metals Manufacturing |
| Pilgrim's Pride Corporation | Greeley | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| Molson Coors Brewing Company | Denver | Manufacturing | Alcoholic Beverages |
| DISH Network Corporation | Englewood | Media and Entertainment | Media and Entertainment Other |
| Arrow Electronics, Inc. | Englewood | Computers and Electronics | Networking Equipment and Systems |
| DaVita, Inc. | Denver | Healthcare, Pharmaceuticals and Biotech | Outpatient Care Centers |
| Blockbuster LLC | Englewood | Media and Entertainment | Media and Entertainment Other |
| CH2M HILL | Englewood | Energy and Utilities | Alternative Energy Sources |
| Newmont Mining Corporation | Greenwood Vlg | Agriculture and Mining | Mining and Quarrying |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Colorado since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Azure programming
- Get your questions answered by easy to follow, organized Azure experts
- Get up to speed with vital Azure programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
