Perl Programming Training Classes in Santa Fe, New Mexico
Learn Perl Programming in Santa Fe, NewMexico and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Perl Programming related training offerings in Santa Fe, New Mexico: Perl Programming Training
Perl Programming Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Linux Fundamentals
23 March, 2026 - 27 March, 2026 - KUBERNETES ADMINISTRATION
23 February, 2026 - 25 February, 2026 - OpenShift Fundamentals
9 February, 2026 - 11 February, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
2 March, 2026 - 6 March, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
26 January, 2026 - 30 January, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
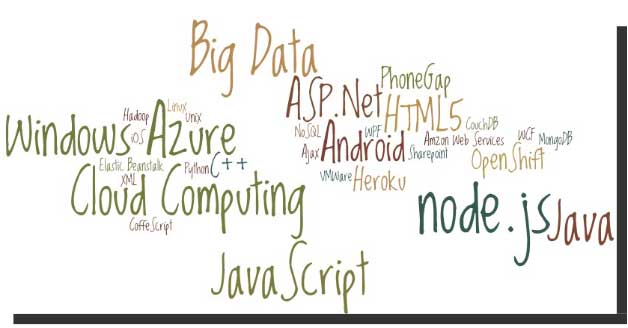
Before we go to the list do you know what makes software skills most sought-after and hence more valuable than most of the other job skills? It is simply because unlike any other skill, software skills are global and are not at all location specific! With the evolution and penetration of internet technologies, the physical distance between the client and service provider hardly matters. So, with more advancement in technology, it is indeed going to rain opportunities on the right skilled developer. I’ll take the liberty to reproduce the following quotes here to prove my claims statistically:
Demand for “cloud-ready” IT workers will grow by 26 percent annually through 2015, with as many as 7 million cloud-related jobs available worldwide.
---IDC White Paper (November 2012).
In the United States, the IT sector is experiencing modest growth of IT jobs in general, with the average growth in IT employment between 1.1 and 2.7 percent per year through 2020.
---U.S. Bureau of Labor Statistics.
 Big data is now in an incredibly important part of how many major businesses function. Data analysis, or the finding of facts from large volumes of data, helps businesses make many of their important decisions. Companies that conduct business on a national or international scale rely on big data in order to plot the general direction of their business. The concept of big data can be very confusing due to the sheer scale of information involved. By following a few simple guidelines, even the layman can understand big data and its impacts on everyday life.
Big data is now in an incredibly important part of how many major businesses function. Data analysis, or the finding of facts from large volumes of data, helps businesses make many of their important decisions. Companies that conduct business on a national or international scale rely on big data in order to plot the general direction of their business. The concept of big data can be very confusing due to the sheer scale of information involved. By following a few simple guidelines, even the layman can understand big data and its impacts on everyday life.
What Exactly is Big Data?
Just about everyone can understand the concept of data. Data is information, and information is everywhere in the modern world. Anytime you use any piece of technology you are making use of data. Anytime you read a book, skim the newspaper or listen to music you are also making use of data. Your brain interprets and organizes data constantly from your senses and your thoughts.
Big data, much like its name infers, simply describes this same data on a large sale. The internet allowed the streaming, sharing and collecting of data on a scale never before imaginable and storage technology has allowed ever increasing hoards of data to be accumulated. In order for something to be considered “big data” it must be at least 10 terabytes or more of information. To put that in perspective, consider that 10 terabytes represents the entire printed collection of material in the Library of Congress. What’s even more remarkable is that many businesses work with far more than the minimum 10 terabytes of data. UPS stores over 16 petabytes of data about its packages and customers. That’s 16,000 terabytes or the equivalent to 1,600 printed libraries of congress. The sheer amount of that data is nearly impossible for a human to comprehend, and analysis of this data is only possible with computers.
How do Big Data Companies Emerge?
All of this information comes from everywhere on the internet. The majority of the useful data includes customer information, search engine logs, and entries on social media networks to name a few. This data is constantly generated by the internet at insane rates. Specified computers and software programs are created and operated by big data companies that collect and sort this information. These programs and hardware are so sophisticated and so specialized that entire companies can be dedicated to analyzing this data and then selling it to other companies. The raw data is distilled down into manageable reports that company executives can make use of when handling business decisions.
The Top Five:
These are the five biggest companies, according to Forbes, in the business of selling either raw data reports or analytics programs that help companies to compile their own reports.
1. Splunk
Splunk is currently valued at $186 million. It is essentially a program service that allows companies to turn their own raw data collections into usable information.
2. Opera Solutions
Opera Solutions is valued at $118 million. It serves as a data science service that helps other companies to manage the raw data that pertains to them. They can offer either direct consultation or cloud-based service.
3. Mu Sigma
Mu Sigma is valued at $114 million. It is a slightly smaller version of Opera Solutions, offering essentially the same types of services.
4. Palantir
Palantir is valued at $78 million. It offers data analysis software to companies so they can manage their own raw data analysis.
5. Cloudera
Cloudera is valued at $61 million. It offers services, software and training specifically related to the Apahce Hadoop-based programs.
The software and services provided by these companies impact nearly all major businesses, industries and products. They impact what business offer, where they offer them and how they advertise them to consumers. Every advertisement, new store opening or creation of a new product is at least somewhat related to big data analysis. It is the directional force of modern business.
Sources:
http://www.sas.com/en_us/insights/big-data/what-is-big-data.html
http://www.forbes.com/sites/gilpress/2013/02/22/top-ten-big-data-pure-plays/
http://www.whatsabyte.com/
Related:
Top Innovative Open Source Projects Making Waves in The Technology World
Is the U.S. the Leading Software Development Country?
How to Keep On Top Of the Latest Trends in Information Technology
Unlike Java, Python does not have a string contains method. Instead, use the in operator or the find method. The in operator finds treats the string as a word list whereas the find method looks for substrings. In the example shown below, 'is' is a substring of this but not a word by itself. Therefore, find recoginizes 'is' in this while the in operator does not.
s = "This be a string"
if s.find("is") == -1:
print "No 'is' here!"
else:
print "Found 'is' in the string."
if "is" in s:
print "No 'is' here!"
else:
print "Found 'is' in the string."
#prints out the following:
Found 'is' in the string
No 'is' here!
Static variables in Python are created as part of the class declaration. By contrast, instance variables are created as part of a regular method and not a classmethod or staticmethod.
class A:
i=3 # static variable
def dosomethingregularmethod(self):
self.k=4 # instance variable
# to access static variables
A.i
Tech Life in New Mexico
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in New Mexico since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Perl Programming programming
- Get your questions answered by easy to follow, organized Perl Programming experts
- Get up to speed with vital Perl Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…