XML Training Classes in Knoxville, Tennessee
Learn XML in Knoxville, Tennessee and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current XML related training offerings in Knoxville, Tennessee: XML Training
XML Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Checking to see if a directory exists and then creating it if it is not present requires a few lines of code. Isn't Python great.  Begin by importing the os module and use the exists and makedirs functions.
Begin by importing the os module and use the exists and makedirs functions.
import os
if os.path.exists(somedirectory):
os.makedirs(somedirectory)
Microsoft has now come up with a surface tablet to compete with the Apple iPad. The Surface is the known as the ‘iPad killer’ and ‘Microsoft iPad’. Microsoft has stuck to production of software till date but this is one of its latest hardware devices that is expected to take over the Apple iPad. This is a new challenge posed by Microsoft to Apple.
The Microsoft Surface saw its official release on 19th June in the city of Los Angeles. It has made a great first impression and seems to be beginning a new start in the competition between the best tablets in the international market. It has 10.6’’ screen and a magnetic cover that can be used as a keyboard and also as a kickstand in order to place the device upright on tables. There has been a paradigm shift in Microsoft’s policy when it decided to do away with the tile-based Metro theme for its Desktop that is almost a trademark with it.
There are many features that make the Surface more like a laptop than like a tablet- the most prominent one being the built- in keyboard that will be useful for business customers. As Microsoft Surface employs Windows 8 as an operating system, which is also used in its computers and laptops, it will be a lot easier for customers to switch among their devices.
The tablet was announced by Microsoft’s CEO, Steve Ballmer, in Los Angeles at a special press conference. It was hailed to be the first of an entirely new family of a number of devices being created and developed by the company. The Surface has a thickness of 9.3mm and weighs 1.5 pounds. It has a kickstand and keyboard for its cover. It is 0.1 mm thinner than the iPad 3, which is the latest iPad from Apple.
 Globalization
Globalization
Globalization is the fundamental force changing IT service delivery and business's competitive activities in almost every vertical market — and thus economies — in some way, shape or form. One might say that globalization is not a new trend and has been commonplace for quite some time now. Yes, but with the changing economic environment globalizations has special implications for the IT outsourcing industry. With developed countries like the U.S. keeping a strict eye on generating local jobs, IT outsourcing especially in Asian countries such as India and China is expected to see globalization brining in big shifts in business strategy
Potential Impact of Globalization
· Increase in near shoring in addition to outsourcing. Near shoring essentially refers to existing IT companies setting up development/delivery centers in Nordic and South American regions in order to offer same time zone services and also bypass the laws governing local hiring
· A truly global delivery model. Service delivery models will have to become more efficient and flexible and work well even if service teams spread across continents
This will mean that large IT outsourcing companies such as TCS will have to expand their presence globally from just having sales offices to actual delivery teams shipping out solutions.
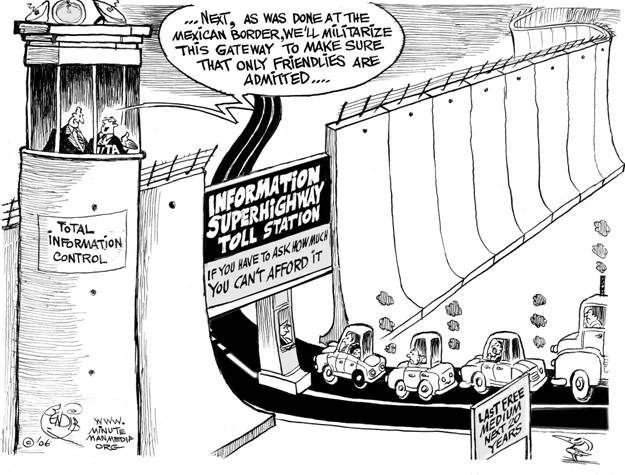
Net Neutrality
You may have heard about net neutrality over the years. Recently, the concept has gone through some changes, and many would consider its underlying principles to be in danger of corruption or dissolution. However, the technical nature of net neutrality ethics makes it difficult to understand for the layperson. Read on, and the central themes and controversies surrounding the principle will be outlined and explained for your convenience.
The Theme
Tech Life in Tennessee
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| First Horizon National Corporation | Memphis | Financial Services | Lending and Mortgage |
| Vanguard Health Systems, Inc. | Nashville | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| The ServiceMaster Company | Memphis | Consumer Services | Consumer Services Other |
| Eastman Chemical Company | Kingsport | Manufacturing | Chemicals and Petrochemicals |
| Brookdale Senior Living, Inc. | Brentwood | Healthcare, Pharmaceuticals and Biotech | Residential and Long-Term Care Facilities |
| Scripps Networks Interactive | Knoxville | Media and Entertainment | Radio and Television Broadcasting |
| Dollar General Corporation | Goodlettsville | Retail | Retail Other |
| IASIS Healthcare Corporation | Franklin | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| Thomas and Betts Corporation | Memphis | Energy and Utilities | Gas and Electric Utilities |
| Tractor Supply Company, Inc. | Brentwood | Retail | Clothing and Shoes Stores |
| TeamHealth, Inc. | Knoxville | Healthcare, Pharmaceuticals and Biotech | Doctors and Health Care Practitioners |
| UNIVERSITY HEALTH SYSTEM, INC. | Knoxville | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| Corrections Corporation of America | Nashville | Business Services | Security Services |
| AutoZone, Inc. | Memphis | Retail | Automobile Parts Stores |
| Mueller Industries, Inc. | Memphis | Manufacturing | Metals Manufacturing |
| UNUM Group | Chattanooga | Financial Services | Insurance and Risk Management |
| Fred's, Inc. | Memphis | Retail | Grocery and Specialty Food Stores |
| International Paper Company | Memphis | Manufacturing | Paper and Paper Products |
| Regal Entertainment Group | Knoxville | Media and Entertainment | Motion Picture and Recording Producers |
| Genesco Inc. | Nashville | Wholesale and Distribution | Apparel Wholesalers |
| Cracker Barrel Old Country Store, Inc. | Lebanon | Retail | Restaurants and Bars |
| Lifepoint Hospitals Inc. | Brentwood | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| FedEx Corporation | Memphis | Transportation and Storage | Postal, Express Delivery, and Couriers |
| Community Health Systems | Franklin | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| HCA Holdings, Inc. | Nashville | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| HealthSpring Inc. | Franklin | Healthcare, Pharmaceuticals and Biotech | Healthcare, Pharmaceuticals, and Biotech Other |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Tennessee since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about XML programming
- Get your questions answered by easy to follow, organized XML experts
- Get up to speed with vital XML programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
