Oracle, MySQL, Cassandra, Hadoop Database Training Classes in Chesapeake, Virginia
Learn Oracle, MySQL, Cassandra, Hadoop Database in Chesapeake, Virginia and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Oracle, MySQL, Cassandra, Hadoop Database related training offerings in Chesapeake, Virginia: Oracle, MySQL, Cassandra, Hadoop Database Training
Oracle, MySQL, Cassandra, Hadoop Database Training Catalog
Cassandra Classes
Hadoop Classes
Linux Unix Classes
MySQL Classes
Oracle Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
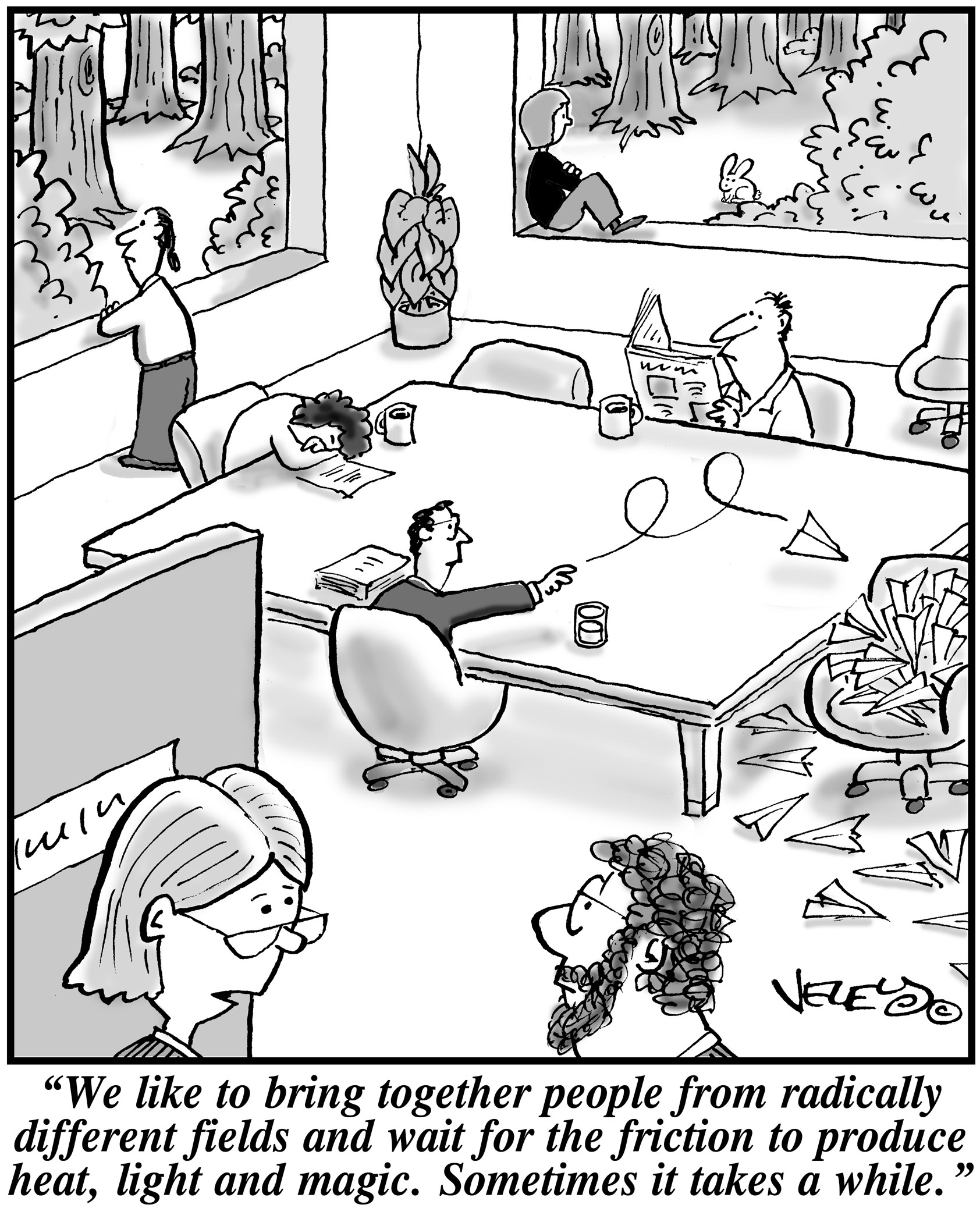 When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
The question is, what is it that great leaders like David Khasidy and Daniel Nigro do that make the difference? How do the most vulnerable companies (start ups) break the mold and become a part of our everyday lives?
It starts with their mission and vision.
Create a Strong Mission and Vision
There are many reasons why start ups fail. For one, they usually lack the capital to last through the lean times. Secondly, they often don't have the tolerance for setbacks that occur. Lastly, they do not have a long-term plan, also called a mission.
When a business has a strong mission, the team knows it and their focus toward their work and service to others within and without the company reflects that. To complement that, the shorter term vision of the company needs to be present as well.
This can even be seen in sole proprietorships with no employees, such as when Brian Pascale started his law practice. His vision was to find justice for his clients while his mission was to build upon a career that had already set precedents in the area of tort law.
As his practice has grown, new staff members can sense the vision and mission he exudes.
Encourage Ownership of Projects and Processes
Start ups need to inspire and motivate their employees because they need to know that they are not only a part of something important, but that their contributions mean something.
What won't happen if they are not there? What contribution do they make, and what are the consequences of them not fulfilling their part of the work?
By encouraging ownership in projects, team members can find that the work they are doing is not only important for the organization, but that they are going to be a big part of what makes it happen. The alternative is that they feel replaceable.
Offer Incentives That Keep the Company Competitive
When team members embrace the mission and vision of the company, and then take ownership for the company's success, they are going to need to be justly rewarded.
This could include flexible schedules (for those who don't need a stringent one), use of an account at a nearby takeout place, or even the potential for ownership as a result of a vesting program.
The incentive everyone is looking for more immediately, though, is cash. When the company takes in more revenue as a result of the efforts of those on the team, rewarding them can go a long way not only in making them feel appreciated, but in encouraging them to bring in more business.
Members of a start up team are usually very talented, and commonly underpaid. However, if they believe they are going somewhere, it will make a big difference.
Related:
Good non-programmer jobs for people with software developer experience
From Brennan's Blog which is no longer up and running:
I use Remote Desktop all the time to work inside of my development systems hosted by Microsoft Virtual Server. I use the host system to browse the web for documentation and searches as I work and when I need to copy some text from the web browser I find many times the link between the host clipboard and the remote clipboard is broken. In the past I have read that somehow the remote clipboard utility, rdpclip.exe, gets locked and no longer allows the clipboard to be relayed between the host and the client environment. My only way to deal with it was to use the internet clipboard, cl1p.net. I would create my own space and use it to send content between environments. But that is a cumbersome step if you are doing it frequently.
The only way I really knew to fix the clipboard transfer was to close my session and restart it. That meant closing the tools I was using like Visual Studio, Management Studio and the other ancillary processes I have running as I work and then restarting all of it just to restore the clipboard. But today I found a good link on the Terminal Services Blog explaining that what is really happening. The clipboard viewer chain is somehow becoming unresponsive on the local or remote system and events on the clipboards are not being relayed between systems. It is not necessarily a lock being put in place but some sort of failed data transmission. It then goes on to explain the 2 steps you can take to restore the clipboard without restarting your session.
- Use Task Manager to kill the rdpclip.exe process
- Run rdpclip.exe to restart it
The clipboard communications should be restored. My clipboard is currently working because I just restarted my session to fix it, but I wanted to test these steps. I killed rdpclip.exe and started it and was able to copy/paste from the remote to the host system. The next time my clipboard dies I will have to check to see if these steps truly do work.
As part of our C++ Tutorials series, here is a tutorial on the tricks of the trade for using C++ I/O. Keep in mind that an application without I/O is just a black box; no communcation is taking place. 
No matter what type of business you’re in, boosting your bottom line is always in the back of your mind. In a rough economy, it can be tempting to focus too much on pulling in more money and not enough on containing it from within.
That’s right, containing it. You have the potential to lose hundreds of thousands of dollars every year right under your nose from something as simple as lack of or ineffective computer training.
How much do the employees you have working for you right now really understand about technology? How good is your IT tech department? Technology changes faster than a blink of an eye and oftentimes, businesses struggle to keep their top employees trained.
With millions of dollars being lost to Internet espionage, file corruption and other computer crimes, staying on top of changes is essential. Recently, online learning centers have been emerging as the go-to method for quick and inexpensive learning. Unfortunately, this type of computer learning isn’t always the best solution.
Tech Life in Virginia
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Brink's Inc. | Richmond | Business Services | Security Services |
| Federal Home Loan Mortgage Corporation (Freddie Mac) | Mc Lean | Financial Services | Lending and Mortgage |
| General Dynamics Corporation | Falls Church | Manufacturing | Aerospace and Defense |
| CarMax, Inc. | Henrico | Retail | Automobile Dealers |
| NVR, Inc. | Reston | Real Estate and Construction | Construction and Remodeling |
| Gannett Co., Inc. | Mc Lean | Media and Entertainment | Newspapers, Books and Periodicals |
| Smithfield Foods, Inc. | Smithfield | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| ManTech International Corporation | Fairfax | Computers and Electronics | IT and Network Services and Support |
| DynCorp International | Falls Church | Manufacturing | Aerospace and Defense |
| Genworth Financial, Inc. | Richmond | Financial Services | Insurance and Risk Management |
| MeadWestvaco Corporation | Richmond | Manufacturing | Paper and Paper Products |
| Dollar Tree, Inc. | Chesapeake | Retail | Department Stores |
| Alpha Natural Resources, Inc. | Abingdon | Agriculture and Mining | Mining and Quarrying |
| SRA International, Inc. | Fairfax | Business Services | Business Services Other |
| NII Holdings, Inc. | Reston | Telecommunications | Wireless and Mobile |
| Dominion Resources, Inc. | Richmond | Energy and Utilities | Gas and Electric Utilities |
| Norfolk Southern Corporation | Norfolk | Transportation and Storage | Freight Hauling (Rail and Truck) |
| CACI International Inc. | Arlington | Software and Internet | Data Analytics, Management and Storage |
| Amerigroup Corporation | Virginia Beach | Financial Services | Insurance and Risk Management |
| Owens and Minor, Inc. | Mechanicsville | Healthcare, Pharmaceuticals and Biotech | Personal Health Care Products |
| Advance Auto Parts, Inc | Roanoke | Retail | Automobile Parts Stores |
| SAIC | Mc Lean | Software and Internet | Software |
| AES Corporation | Arlington | Energy and Utilities | Gas and Electric Utilities |
| Capital One Financial Corporation | Mc Lean | Financial Services | Credit Cards and Related Services |
| Sunrise Senior Living, Inc. | Mc Lean | Healthcare, Pharmaceuticals and Biotech | Residential and Long-Term Care Facilities |
| Computer Sciences Corporation | Falls Church | Software and Internet | Software |
| Altria Group, Inc. | Richmond | Manufacturing | Manufacturing Other |
| Northrop Grumman Corporation | Falls Church | Manufacturing | Aerospace and Defense |
| Alliant Techsystems Inc. | Arlington | Manufacturing | Aerospace and Defense |
| Markel Corporation | Glen Allen | Financial Services | Insurance and Risk Management |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Virginia since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Oracle, MySQL, Cassandra, Hadoop Database programming
- Get your questions answered by easy to follow, organized Oracle, MySQL, Cassandra, Hadoop Database experts
- Get up to speed with vital Oracle, MySQL, Cassandra, Hadoop Database programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

