Oracle, MySQL, Cassandra, Hadoop Database Training Classes in Gainesville, Florida
Learn Oracle, MySQL, Cassandra, Hadoop Database in Gainesville, Florida and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Oracle, MySQL, Cassandra, Hadoop Database related training offerings in Gainesville, Florida: Oracle, MySQL, Cassandra, Hadoop Database Training
Oracle, MySQL, Cassandra, Hadoop Database Training Catalog
Cassandra Classes
Hadoop Classes
Linux Unix Classes
MySQL Classes
Oracle Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Checking to see if a file exists is a two step process in Python. Simply import the module shown below and invoke the isfile function:
import os.path
os.path.isfile(fname)
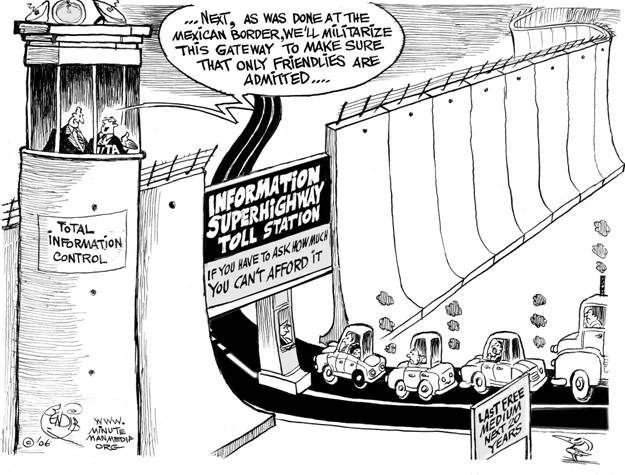
Net Neutrality
You may have heard about net neutrality over the years. Recently, the concept has gone through some changes, and many would consider its underlying principles to be in danger of corruption or dissolution. However, the technical nature of net neutrality ethics makes it difficult to understand for the layperson. Read on, and the central themes and controversies surrounding the principle will be outlined and explained for your convenience.
The Theme
Communication is one of the main objectives that an organization needs to have in place to stay efficient and productive. A breakdown in accurate and efficient communication between departments at any point in the organization can result in conflict or loss of business. Sadly, the efficiency between different departments in an organization becomes most evident when communication breaks down. As an example, David Grossman reported in “The Cost of Poor Communications” that a survey of 400 companies with 100,000 employees each cited an average loss per company of $62.4 million per year because of inadequate communication to and between employees.
With the dawning of the big-data era and the global competition that Machine Learning algorithms has sparked, it’s more vital than ever for companies of all sizes to prioritize departmental communication mishaps. Perhaps, today, as a result of the many emerging markets, the most essential of these connections are between IT and the business units. CMO’s and CIO’s are becoming natural partners in the sense that CMO’s, in order to capture revenue opportunities, are expected to master not just the art of strategy and creativity but also the science of analytics. The CIO, on the other hand, is accountable for using technical groundwork to enable and accelerate revenue growth. Since business and technology people speak very different languages, there’s a need on both sides to start sharing the vocabulary or understanding of what is expected in order to avoid gridlock.
In the McKinsey article, Getting the CMO and CIO to work as partners, the author speaks to five prerequisite steps that the CMO and the CIO can take in order to be successful in their new roles.
--- Be clear on decision governance
Teams should define when decisions are needed, what must be decided, and who is responsible for making them.
The world of technology moves faster than the speed of light it seems. Devices are updated and software upgraded annually and sometimes more frequent than that. Society wants to be able to function and be as productive as they can be as well as be entertained “now”.
Software companies must be ready to meet the demands of their loyal customers while increasing their market share among new customers. These companies are always looking to the ingenuity and creativity of their colleagues to keep them in the consumer’s focus. But, who are these “colleagues”? Are they required to be young, twenty-somethings that are fresh out of college with a host of ideas and energy about software and hardware that the consumer may enjoy? Or can they be more mature with a little more experience in the working world and may know a bit more about the consumer’s needs and some knowledge of today’s devices?
Older candidates for IT positions face many challenges when competing with their younger counterparts. The primary challenge that most will face is the ability to prove their knowledge of current hardware and the development and application of software used by consumers. Candidates will have to prove that although they may be older, their knowledge and experience is very current. They will have to make more of an effort to show that they are on pace with the younger candidates.
Another challenge will be marketing what should be considered prized assets; maturity and work experience. More mature candidates bring along a history of work experience and a level of maturity that can be utilized as a resource for most companies. They are more experienced with time management, organization and communication skills as well as balancing home and work. They can quickly become role models for younger colleagues within the company.
Unfortunately, some mature candidates can be seen as a threat to existing leadership, especially if that leadership is younger. Younger members of a leadership team may be concerned that the older candidate may be able to move them out of their position. If the candidate has a considerably robust technological background this will be a special concern and could cause the candidate to lose the opportunity.
Demonstrating that their knowledge or training is current, marketing their experience and maturity, and not being seen as a threat to existing leadership make job hunting an even more daunting task for the mature candidate. There are often times that they are overlooked for positions for these very reasons. But, software companies who know what they need and how to utilize talent will not pass up the opportunity to hire these jewels.
Related:
H-1B Visas, the Dance Between Large Corporations and the Local IT Professional
Is a period of free consulting an effective way to acquire new business with a potential client?
Tech Life in Florida
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Lender Processing Services, Inc. (LPS) | Jacksonville | Software and Internet | Data Analytics, Management and Storage |
| World Fuel Services Corporation | Miami | Energy and Utilities | Gasoline and Oil Refineries |
| SEACOR Holdings Inc. | Fort Lauderdale | Transportation and Storage | Marine and Inland Shipping |
| MasTec, Inc. | Miami | Business Services | Security Services |
| Health Management Associates, Inc. | Naples | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| B/E Aerospace, Inc. | Wellington | Manufacturing | Aerospace and Defense |
| Roper Industries, Inc. | Sarasota | Manufacturing | Manufacturing Other |
| AutoNation | Fort Lauderdale | Retail | Automobile Dealers |
| Watsco, Inc. | Miami | Wholesale and Distribution | Wholesale and Distribution Other |
| SFN Group | Fort Lauderdale | Business Services | HR and Recruiting Services |
| Tupperware Corporation | Orlando | Manufacturing | Plastics and Rubber Manufacturing |
| AirTran Holdings, Inc. | Orlando | Travel, Recreation and Leisure | Passenger Airlines |
| WellCare Health Plans, Inc. | Tampa | Healthcare, Pharmaceuticals and Biotech | Healthcare, Pharmaceuticals, and Biotech Other |
| Lennar Corporation | Miami | Real Estate and Construction | Real Estate Agents and Appraisers |
| HSN, Inc. | Saint Petersburg | Retail | Retail Other |
| Certegy | Saint Petersburg | Business Services | Business Services Other |
| Raymond James Financial, Inc. | Saint Petersburg | Financial Services | Trust, Fiduciary, and Custody Activities |
| Winn-Dixie Stores, Inc. | Jacksonville | Retail | Grocery and Specialty Food Stores |
| Jabil Circuit, Inc. | Saint Petersburg | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| CSX Corporation | Jacksonville | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Fidelity National Financial, Inc. | Jacksonville | Financial Services | Insurance and Risk Management |
| Tech Data Corporation | Clearwater | Consumer Services | Automotive Repair & Maintenance |
| TECO Energy, Inc. | Tampa | Manufacturing | Chemicals and Petrochemicals |
| Lincare Holdings Inc | Clearwater | Healthcare, Pharmaceuticals and Biotech | Medical Supplies and Equipment |
| Chico's FAS Inc. | Fort Myers | Retail | Clothing and Shoes Stores |
| Burger King Corporation LLC | Miami | Retail | Restaurants and Bars |
| Publix Super Markets, Inc. | Lakeland | Retail | Grocery and Specialty Food Stores |
| Florida Power and Light Company | Juno Beach | Energy and Utilities | Gas and Electric Utilities |
| Ryder System, Inc. | Miami | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Citrix Systems, Inc. | Fort Lauderdale | Software and Internet | Software and Internet Other |
| Harris Corporation | Melbourne | Telecommunications | Wireless and Mobile |
| Office Depot, Inc. | Boca Raton | Computers and Electronics | Audio, Video and Photography |
| Landstar System, Inc. | Jacksonville | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Darden Restaurants, Inc. | Orlando | Retail | Restaurants and Bars |
| PSS World Medical, Inc. | Jacksonville | Healthcare, Pharmaceuticals and Biotech | Medical Supplies and Equipment |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Florida since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Oracle, MySQL, Cassandra, Hadoop Database programming
- Get your questions answered by easy to follow, organized Oracle, MySQL, Cassandra, Hadoop Database experts
- Get up to speed with vital Oracle, MySQL, Cassandra, Hadoop Database programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
